Earn your visitors' trust.
Address the security and trust concerns that cost you sales and convert more customers at every stage of the buyer’s journey with TrustedSite's earned certification program.
Get Certified Watch the Video
Address the security and trust concerns that cost you sales and convert more customers at every stage of the buyer’s journey with TrustedSite's earned certification program.
Get Certified Watch the Video
Trusted by over 100,000 businesses of all sizes





Our process starts with certifying key issues like security, business integrity, and merchant reliability. As you earn our certifications, you can begin displaying them on your site with trustmarks.
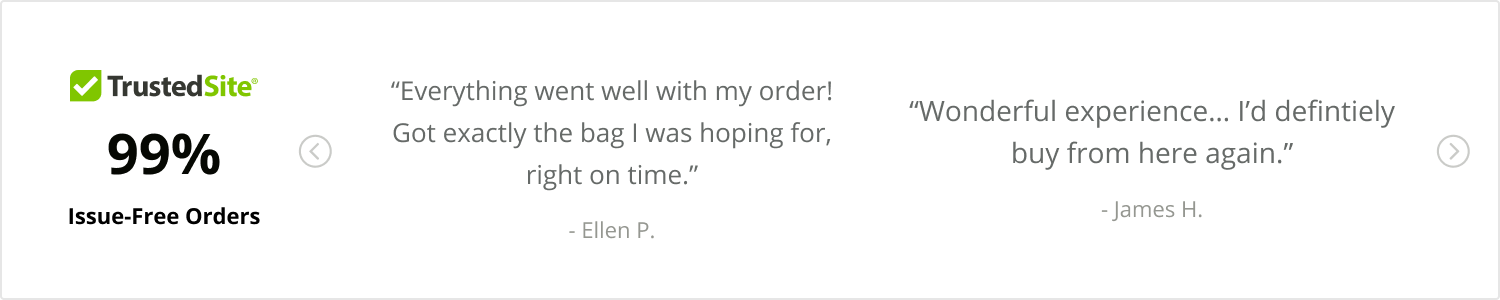
Sites that use our trustmarks see conversion increases as high as 30%.
Explore our Certifications →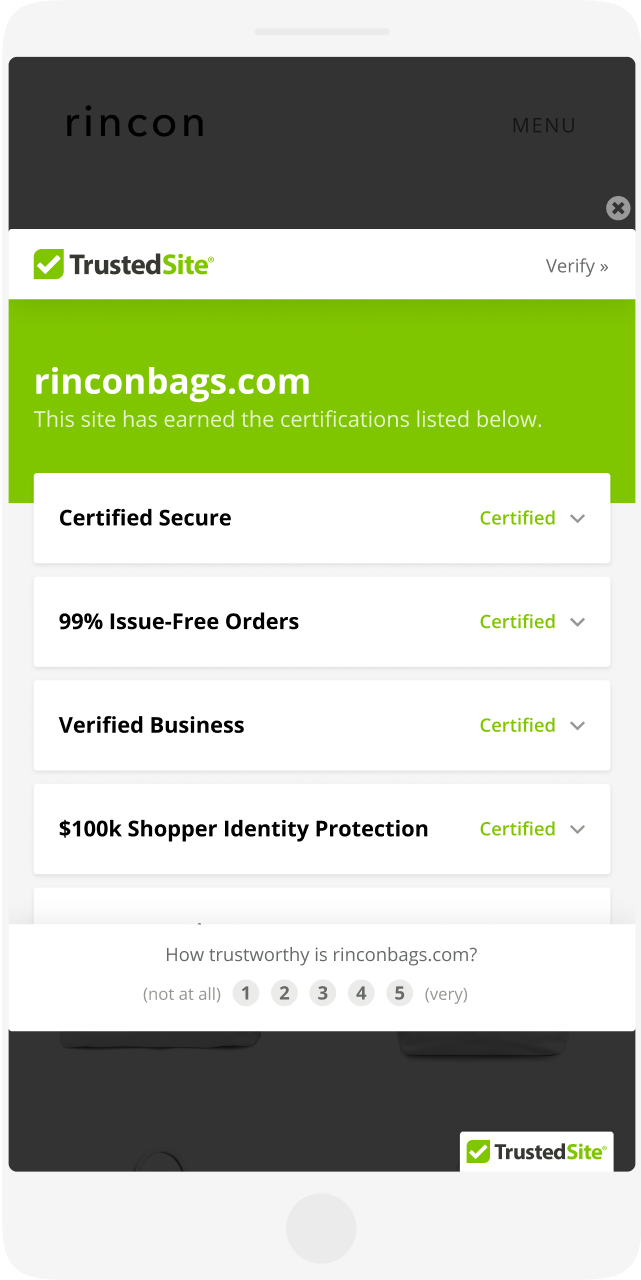

You work hard to drive new traffic to your website, but nearly half of consumers have abandoned shopping carts because of concerns about business legitimacy. If you’re not addressing visitor concerns, your customer acquistion efforts may be futile.
See the Consumer Trust Data → 97% of consumers are concerned about shopping on unfamiliar sites
97% of consumers are concerned about shopping on unfamiliar sites
Our trustmarks and certifications are designed to alleviate the biggest concerns shoppers have on their path to purchase.






TrustedSite trustmarks work together to build visitor trust throughout the customer journey. They’re quick to install and easy to customize.
Add to my site Learn MoreSites that have tested TrustedSite Certification have seen 2-30% higher conversion rates.
See the results →

“Working with TrustedSite has been an easy and informative process. The A/B test clearly showed that our conversion rates were improved with TrustedSite as a trust factor on our site.”
- Collin Jarvis, Vice President of Stealth Belt.Eliminate issues like missing images and broken links.
Learn MoreAutomate sitemap generation & submission.
Learn More
Even well-known brands can benefit from third-party trust-building tools. See how TrustedSite helped Holabird Sports build trust and boost sales.
Read the Case Study →