Skyhigh Secure Web Gateway (SWG)
Intelligent Web Security for Your Extended Workforce
Infinitely scale, connect and secure your workforce while accessing the internet from anywhere, any application, any device and at anytime.
Intelligent Defense Against Modern Threats
Skyhigh AI stands as your ultimate defense, ensuring seamless and safe collaboration from any device, anywhere. Elevate your cybersecurity strategy and experience with the transformative power of our cutting-edge solutions.
Learn More
No matter where you are on the SWG spectrum we have you covered
Simplify your web security with one console

On-Premises SWG
Ensure regulatory compliance with the trusted on-premises appliance used by enterprises worldwide

Hybrid SWG
Support your migration to the cloud with a hybrid approach

Cloud SWG
Evolve to the most complete cloud-based delivered web security
Web Security Built for the Cloud
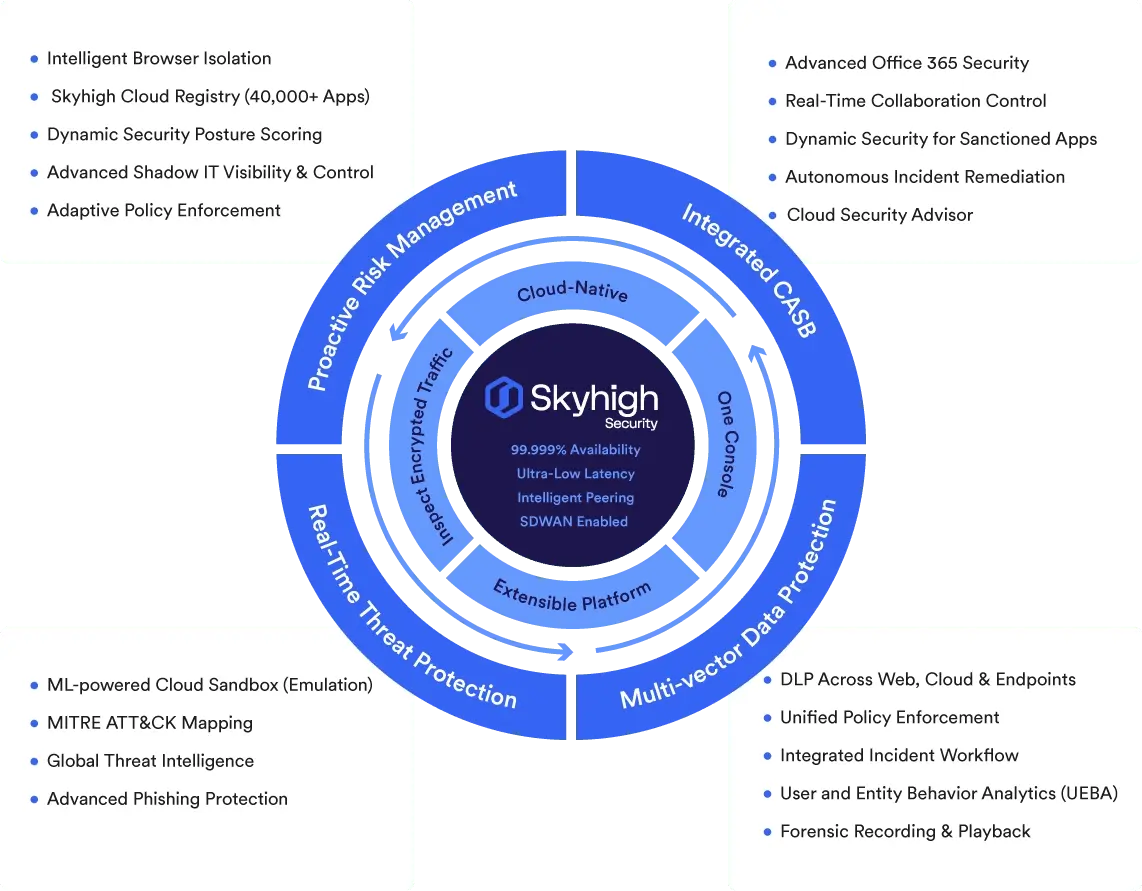
The most complete solution protecting both users and data.
Skyhigh SWG
With integrated RBI, CASB, and industry leading DLP capabilities
Protection From Unknown Threats
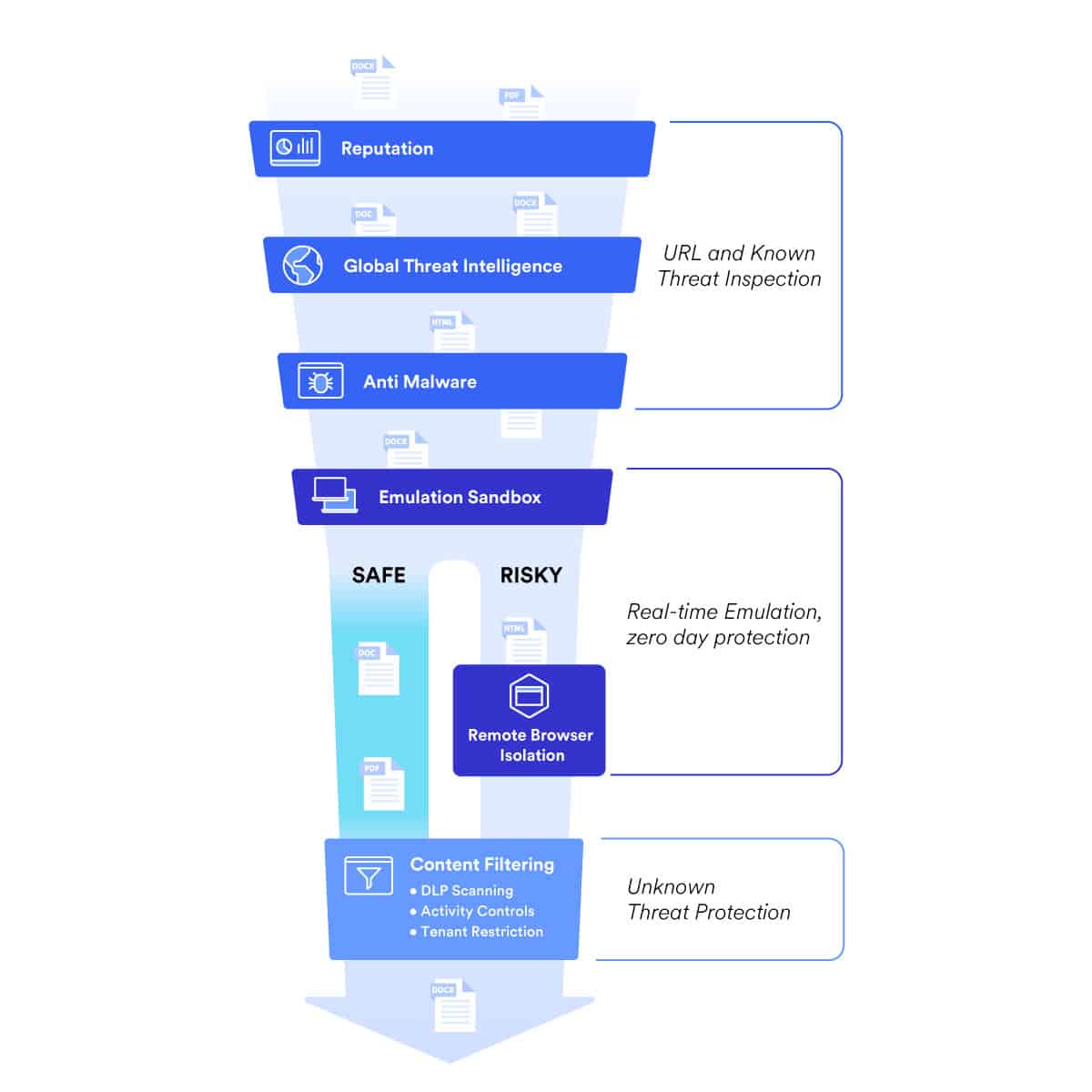
Stop advanced malware and sophisticated threats from ever reaching your users with multi-layer security and fully integrated Remote Browser Isolation (RBI), without impacting the user experience and at no extra cost.
Application Visibility and Control
Integrate with CASB’s cloud registry to block access to non-secure or not corporate web sites and cloud apps based on categories, reputation, or risk.
Advanced Data Protection
Remain regulation compliant and prevent the exfiltration of sensitive data while accessing the internet with the most advanced Data Loss Prevention (DLP) engine on the market.
Secure Web Gateway Use Cases
Skyhigh Secure Web Gateway enables organizations to connect and secure their workforce wherever they are located. Some of the most common use cases are:
-
- Blocking user access to websites
-
- Protecting against advanced cyber attacks
-
- Protecting against new or unknown websites
-
- Achieving visibility into encrypted web traffic
Product Features & Capabilities
What you can expect from Skyhigh SWG
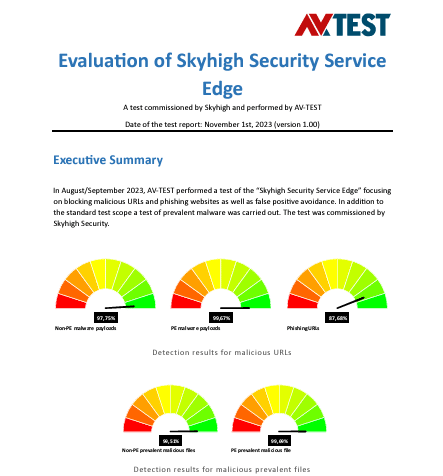
Detect zero-day threats in real time with a powerful combination of machine learning, RBI, inline emulation-based sandboxing and to-the-minute global threat intelligence capabilities.
Assign websites to categories of high, medium, low and unverified risk with built-in threat intelligence that evaluates a website’s reputation based on past behavior and filter or block access to specific types of media or malicious content
Protect against threats entering and sensitive data leaving your organization by inspecting encrypted traffic - regardless of the user's connection method or location.
Access the entire portfolio of Skyhigh solutions from a single cloud platform.
An integrated option to egress traffic via dedicated IPs that are unique to you. Experience the benefits of a dedicated egress IP, including: maintaining traffic control, remaining compliant, and managing your IP reputation.
Empower a more productive workforce with virtually no end-user service disruption. Skyhigh SWG is infinitely scalable and delivers 99.999% uptime to support remote working and a distributed digital ecosystem.
Skyhigh Security + Trellix IVX
Take your security posture to the next level with the powerful integration between Skyhigh Security and Trellix IVX
Press Release: Skyhigh + Trellix Integration
Read our press release announcing this exciting integration that provides an additional layer of security with Skyhigh SWG for Cloud.
Webinar: Stop Evolving Threats in Their Tracks
This webinar details how to neutralize sophisticated attacks with the industry-leading protection of Skyhigh and the next-generation sandboxing of Trellix IVX.
Demo: Skyhigh SWG + Trellix IVX
This short demo demonstrates how this integration forms a robust defense system, offering a multi-layer approach to detect, isolate, and mitigate cyber threats effectively.
Web Security Built for the Cloud
Zero-day malware protection & multi-layer securityEnhance visibility and process traffic for unauthorized access, data risk and threats from anywhere in the world, without compromising security, speed or connectivity.
Awards and Recognition
Resources