As technology makes our lives increasingly convenient, we rely on it more. We use it constantly nowadays, even entrusting our personal information to apps and services. But cybercriminals know that—in fact, they count on it. The McAfee Labs Threats Report, September 2016, reveals that crooks are getting personal, targeting individuals’ data more than ever. It’s gotten easier for them to nab this information, and the report even states “personal information about customers or employees now makes up the majority of breaches reported, with payment info a distant third.”
But why is that happening? Shouldn’t advances in technology make us safer? Truth be told, while it can, new vehicles for sharing personal data can also be treasure coves for criminals.
We’re in an age where mobile phones, cloud sharing platforms, and social media are the norm. That’s largely the reason why personal data has become such a big target. But it’s important to remember that, as much as new technology invites threats, so does older technology. It’s all about ease of access: when attackers see a cybersecurity system (old or new) with loopholes, they’re enticed.
One of the latest cybercriminal ventures? Believe it or not, it’s medical data. Hospital software and technology is more outdated than you think. But cybercriminals dig even deeper than consumers, and they’ve taken advantage of weaknesses, especially in the past year. This year, hospitals have grown to be a massive target for ransomware, with one cybercriminal even gaining $121 million dollars from a handful of campaigns against hospitals.
This increase in ransomware attacks on the healthcare industry isn’t random. It’s due to dated infrastructures that are required to be operational at all times. These systems struggle to integrate new cybersecurity technology with antiquated systems—they’re sitting ducks.
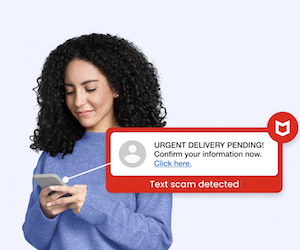
While hospitals contain reservoirs of personalized data, many thieves also going straight to consumers. Age isn’t the only factor; new technologies are also being exploited. Take our use of social media as an example. It provides thieves with a new source for directing and enhancing phishing attacks. Other new platforms, such as cloud technologies, are also harder to protect using old methods. With more of people’s time spent on mobile, crooks are capitalizing there as well. In the second quarter of this 2016 alone, the number of new mobile malware came in as the highest ever recorded at 2,000,000 samples.
The moral of the story is this: personal data is being hunted. Crooks are finding security gaps, in both new and old technologies, to extract the most private of information.
But luckily, there’s a silver lining—IT security is also thinking ahead. The industry is constantly looking into new, inventive ways to keep people safe. As the latest McAfee Labs Threat Report has indicated, the amount of devices connected to the internet and the volume of data increases every year. That allows analytics to slowly become the primary approach to disrupt incoming attacks. From data science to machine learning, we can expect more improved state-of-the-art security solutions day by day.
In fact, we’ve already started. With the release of the McAfee Next Generation Anti-Malware Engine, the centerpiece in our new consumer security lineup, we’re using behavioral analytics and machine learning to better detect threats. This new solution, along with our other product updates, ensures that your mobile, cloud-connected, and wearable technology devices stay secure.
Tips to Protect Your Personal Data
Meanwhile, to better safeguard your personal data, here are a few tips to protect yourself:
- Time for an upgrade. Don’t let your own records be like that of outdated hospitals. It is critical that you steer clear of having old and susceptible software. Upgrade your devices’ operating systems to the latest versions. More often than not, software updates come with updated security.
- Have security on your mind when purchasing new technology or accessing a website. Do a quick Google search for a product before you take it home, and make sure its security standing is up to par. Also check what security settings it features. If you’re concerned an individual website is weak, you can use the updated True Key app so you can securely log in.
- Securely back everything up and be ready for removal. When breaches do happen, damage control is necessary. Having information for your accounts can help you communicate to responsible security teams. So keep copies on an external hard drive. That way, if there is a breach, you don’t lose everything. And if malware is deployed, we promise you won’t be infected for long—our new Virus Protection Pledge products guarantee 100% virus removal or your money back.
And of course, stay on top of the latest consumer and mobile security threats by following me and @McAfee on Twitter, and Like us on Facebook.