This blog post was written by Bruce Snell.
Next month I’ll be moving back to the US after a few years living in Japan. While moving internationally can be a headache, one of the fun things about it is shopping for a new car. I’ve had my eye on a Jeep Wrangler and have been weighing the pros and cons of getting an aftermarket stereo. So I just had to laugh when I woke up and saw the headline, “Hackers Remotely Kill a Jeep on the Highway: With Me in It.” The story discussed how two security researchers successfully demonstrated a remote hack against a moving vehicle.
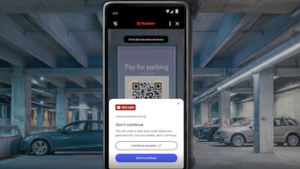
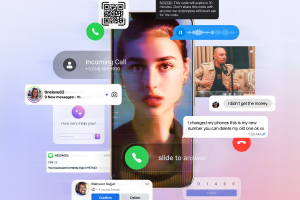
The researchers took advantage of vulnerabilities in order to access the vehicle’s control system—more specifically, through the cellular component of the Uconnect infotainment system. While having a cellular connection provides several benefits, such as remote unlock and real-time traffic information, it was used in this instance to get into the on-board systems of the car.
The researchers used a vulnerability in the Uconnect software to overwrite the firmware of the headunit, allowing them full access to the communication system (known as the CAN bus) of the entire car. After that, they were able to do some fairly serious stuff. In a video demo, the researchers started by setting off minor annoyances like turning the AC on full blast, or changing the radio channel and controlling volume.
More alarmingly however, they were also able to remotely disengage the transmission, leaving the Jeep coasting along while on the freeway. While the car was in reverse in a parking lot, they were able to take over the steering controls and even disable the brakes. This was likely done by utilizing code designed for parking assist. All in all, this experiment can teach us something are very serious: hackers do, in fact, have the ability to access a vehicle through the internet.
A few years ago, I was leading a small team to do some research on the potential hacks against automotive targets. We made a lot of interesting discoveries, and at the time, there was nothing you could really accomplish remotely. Sure, there were hacks you could run if you had direct access to the CAN bus. However, since this all happened before cellular vehicle connections were widely used, there was no serious threat. Following our research, we spoke with people in the automotive industry about our findings, and reassuringly, we found they were already doing their own research into potential issues. Of course, you can design what you think is a very secure system, but there is always a way in. Usually that way in is the Internet. That being said, there’s a good reason highly secured systems have no Internet connection.
So, what can we do about this issue?
Thankfully, these researchers were working with Fiat Chrysler for nine months before announcing a recent vulnerability, and a patch is already available. If you have a Chrysler vehicle from late 2013 through early 2015 with Uconnect, you may be at risk.
Owners of vehicles that fit this description should check to see if their car is affected, here. From that site you can find the instructions to download and install the update yourself using a USB thumb drive. You can also take your to your local service department to get the update installed.
I understand that some people still take computer security lightly, but let’s face it—crashing your computer and crashing your car are two dramatically different things.