If you grew up before, or even during the 90s, you were familiar with a world of cords. A cord for the telephone, a cord for the CD player and a cord — of course — for the internet. But around the late 80s and early 90s, things started to change. Cashier systems gained a new feature called WaveLAN. By 1999, the Wi-Fi Alliance was formed and the standard for the vast majority of our communications today was firmly established.
Wi-Fi is easily the defining feature of our modern society. Wi-Fi is advertised in cafés, and friends share login passwords far too often. One of the reasons why Wi-Fi has grown so much in use — other than its massive convenience — is that it can be relatively secure thanks to two common features called “Wi-Fi Protected Access” and “Wi-Fi Protected Access II.” In a nutshell, it established the standard use of security protocols that massively increased the security around data packets and their transmission over wireless networks. The end result are secure Wi-Fi networks relatively free of eavesdroppers.
That is, until today. Cybersecurity researchers have developed a proof-of-concept attack — named KRACK — enabling theoretical baddies to intercept and decipher data, including passwords and messages, that should not be decipherable. It gets worse. According to Ars Technica, which broke the story late on Sunday, these theoretical baddies could also “inject ransomware or other malicious content into a website.” Meaning, a trusted website could appear to be offering a link or advertisement, which actually leads to malware or other malicious content.
Because this vulnerability deals with Wi-Fi standards, almost every device is vulnerable. But, given the proof-of-concept attack can only succeed under particular conditions, some caveats are in order. (As a note, “proof-of-concept attack” is an industry term signifying this particular vulnerability was first discovered and tested in academic and-or industrial research environments and that no cybercriminal has used it to anyone’s knowledge thus far.)
First, we need to understand this attack affects the WPA2 Wi-Fi network standard, which is the more advanced version of WPA. Second, we also need to understand it exploits vulnerabilities in a “four-way handshake.” It’s complicated concept, but, in a nutshell, it ensures every device is what it says, through the use of specific keys that are shared through handshakes. It’s as if you were trying to get into a secret society but had to know four different secret handshakes in order to get through the door.
The problem with KRACK is that it essentially tricks its victims — in this case, computers, not users — into reinstalling a new, but already-in-use, key. It appears to send a signal to reset seemingly random figures to those that the attacker knows. By doing so, the attacker can infiltrate the club (in this analogy, your network).
Now, for those caveats I mentioned. In order for this attack to succeed, it has to be in range of a targeted Wi-Fi network. Meaning a cybercriminal would have to park outside your house for a while to successfully attack your network. While possible, it’s also very unlikely.
This attack also affects some operating systems (the software used to make your computer run, like Windows, Mac OS, Android) more than others. The most vulnerable operating systems are Linux and Android. Additionally, a targeted network must remain in place long enough for the attack to transpire (which can be as little as a few seconds). This means that large Wi-Fi networks can be attacked. It also means that connected devices are vulnerable as well.
Tips to Protect Yourself
So, what can you do to protect yourself? Well, it largely depends on how quickly manufacturers and software developers can release patches to fix these vulnerabilities. Still, there are steps you can take to protect yourself:
- Update your device’s software. There will be a number of updates issued over the coming weeks and months, for phones and other devices, in order to address the vulnerabilities KRACK has exposed. Implement these updates as soon as you can.
- Update your router’s firmware. Your router is going to the be the most critical device in securing your wireless network. Again, you’re largely at the mercy of how fast device manufacturers and software developers generate a patch. Check your respective device manufacturer’s website for the details and status of the KRACK patch.
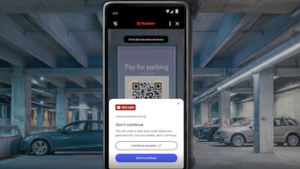
- Consider a VPN. If your employer has given you a device to work from, they’ve likely given you a VPN to use as well. A Virtual Private Network, such as McAfee Safe Connect, can help to secure and encrypt your data on public Wi-Fi networks. It can also help secure your data while patches are generated for this vulnerability. Be aware, however: router-driven security features, like those found in McAfee Secure Home Platform will not protect your wireless and IoT devices, as KRACK targets the data exchanged between routers and devices — only an update to router will fix this issue.
For more details on the KRACK vulnerability, check our these blogs by our McAfee Labs team. And, of course, stay on top of the latest consumer and mobile security threats by following me and @McAfee_Home on Twitter, and ‘Like’ us on Facebook.