We kicked off 2018 with two powerful new exploits: Meltdown and Spectre. And since the discovery of Meltdown and Spectre on January 3rd, vendors have been hard at work issuing patches to remedy their nasty side effects – with the majority supplying fixes within the first week. But, unfortunately, some malware makers have still found ways to leverage a handful of these exploits. In fact, according to the AV-Test Institute, there are currently 139 malware samples out in the wild that appear to be related to the recently reported CPU exploits and have been designed to attack web browsers running JavaScript.
So, why is this still happening? Though operating system vendors, chip makers, and browser makers have released patches to mitigate the attacks, that doesn’t exactly mean all systems everywhere have been locked down, especially as new malware strains continue to emerge. In fact, the CVE-2017-5715, CVE-2017-5753, and CVE-2017-5754 exploits are still being abused by cybercriminals, who are leveraging them to potentially attack browsers that support JavaScript and WebAssembly.
Tips to Secure Your Personal Info
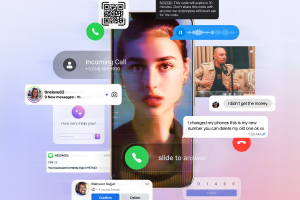
What’s more – if they successfully infiltrate these browsers, cybercriminals can steal passwords and other personal data. So, it’s crucial users are vigilant and take the necessary precautions to secure their personal info while surfing the web. To do just that, follow these tips:
- Exit out of your browser window. If you’re not actively using your browser window, close it. This should decrease your chances for attack and also conserve energy in the process.
- Update everything regularly. Along with updating every type of device impacted by Meltdown and Spectre, be sure to update your browser as soon as an update becomes available. That way, you can apply any additional patches that are created to combat these new malware attacks.
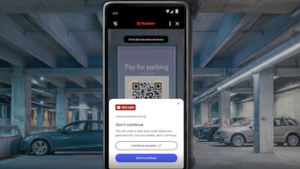
- Surf the web safely. As I noted in my last post about Meltdown and Spectre, McAfee products are not affected by this exploit. Therefore, after you’ve updated your devices with the latest security software, it’s time to take the next step in personal security by locking down your browser as well. You can do that by installing McAfee WebAdvisor, which acts your own personal safety advisor for your online activity.
And, of course, stay on top of the latest consumer and mobile security threats by following me and @McAfee_Home on Twitter, and ‘Like’ us on Facebook.