As we continue to evolve technologically, so do cybercriminals in their never-ending quest to exploit vulnerabilities in our digital lives. The previous years have clearly shown that cybercriminals are increasingly leveraging new technologies and trends to trick their victims. As we move into another year, it’s crucial to be aware of the tried and tested tactics these cyber criminals use and stay prepared against potential threats.
In this article, we delve deeper into one such tactic that remains a favorite among cybercriminals – ‘phishing‘ via emails. We focus on the trickiest and most dangerous email subject lines that have been commonly used in worldwide phishing emails. Recognizing these ‘ baits’ can be your first step towards safeguarding your identity and valuables against cybercriminals. Beware, there are plenty of these ‘phishes’ in the sea, and it helps to be on your guard at all times.
Understanding the Threat: Email Phishing
Sending email messages filled with malicious links or infectious attachments remains a dominant strategy among cybercriminals. This strategy, commonly known as ‘phishing,’ is often disguised in a variety of forms. The term ‘Phishing’ is derived from the word ‘Fishing,’ and just like fishing, where bait is thrown in the hope that a fish will bite, phishing is a cyber trick where an email is the bait, and the unsuspecting user is the fish.
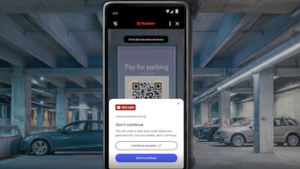
Today’s most common phishing scams found by McAfeerevealed that cybercriminals tend to use certain email subject lines more often. Although this does not mean that emails with other subject lines are not harmful, being aware of the most commonly used ones can give you an edge. The key takeaway here is to be vigilant and alert when it comes to all kinds of suspicious emails, not just those with specific subject lines.
Top 5 Most Dangerous Email Subject Lines
Let’s take a look at the top five most commonly used subject lines in worldwide phishing emails. The list will give you an understanding of the varied strategies employed by cybercriminals. The strategies range from social networking invitations to ‘returned mail’ error messages and phony bank notifications. Be aware that these are just the tip of the iceberg and cyber criminals are continuously coming up with new and improved tactics to gain access to your sensitive data.
- “Invitation to connect on LinkedIn”
- “Mail delivery failed: returning message to sender”
- “Dear [insert bank name here] Customer”
- “Comunicazione importante”
- “Undelivered Mail Returned to Sender”
In the past, cybercriminals used to cast big, untargeted nets in the hopes of trapping as many victims as possible. However, recent trends indicate a shift towards more targeted and custom messages designed to ensnare more victims. A classic example of such a targeted phishing attack is the JP Morgan Chase phishing scam that took place earlier this year.
→ Dig Deeper: Mobile Bankers Beware: A New Phishing Scam Wants Your Money
The fact that phishing scams are still on the rise amplifies the importance of proactive measures to protect our digital assets. As technology advances, these threats continue to evolve, making ongoing vigilance, education, and caution in our online engagements critical in combating the increasing prevalence of such scams.
What Phishing Emails Seek: Your Identity and Wallet
Phishing emails, often with a guise of urgency or familiarity, cunningly aim to deceive recipients into revealing sensitive information, most commonly, personal identities and financial credentials. These malicious messages are designed to prey on our trust and curiosity, making it crucial to scrutinize each email carefully. Cybercriminals behind phishing schemes are after the keys to both your digital identity and your wallet. They may seek login credentials, credit card details, social security numbers, and other sensitive data, which can lead to identity theft, financial loss, and even broader security breaches. It is essential to exercise caution and rely on best practices for email and internet security to thwart their efforts and safeguard your online presence.
While phishing emails come in a variety of forms, their ultimate goal remains the same: to steal your identity and money. As we move into the New Year, it’s prudent to add a few safety measures to your resolutions list. Protecting yourself from the increasingly sophisticated and customized phishing attacks requires more than awareness.
Avoiding Phishers’ Techniques
With an understanding of phishing techniques, the next step is learning how to protect yourself from falling prey to them. Ultimately, you are the first line of defense. If you’re vigilant, you can prevent cyber criminals from stealing your sensitive information. The following are some tips that can help you safeguard your digital life and assets:
First, avoid opening attachments or clicking on links from unknown senders. This is the primary method that cybercriminals use to install malware on your device. If you don’t recognize the sender of an email, or if something seems suspicious, don’t download the attachment or click on the link. Even if you do know the sender, be cautious if the email message seems odd or unexpected. Cybercriminals often hack into email accounts to send malicious links to the victim’s contacts.
Another important practice is to think twice before sharing personal information. If you’re asked for your name, address, banking information, password, or any other sensitive data on a website you accessed from an email, don’t supply this information, as it is likely a phishing attempt. In case of any doubts regarding the authenticity of a request for your information, contact the company directly using a phone number or web address you know to be correct.
Safeguarding Your Digital Life
Even with the most diligent practices, it’s still possible to fall victim to phishing attacks. Hence, having security nets in place is crucial. Start by being careful on social networks. Cybercriminals often hack into social media accounts and send out phishing links as the account owner. Even if a message appears to come from a friend, be cautious if it looks suspicious, especially if it contains only a link and no text.
Installing comprehensive security software is another essential step. McAfee LiveSafe service, for instance, offers full protection against malware and viruses on multiple devices. This software can be a lifeline if you happen to click a malicious link or download a hazardous attachment from an email.
It’s also a smart idea to regularly update your devices. Updates often contain patches for security vulnerabilities that have been discovered since the last iteration of the software. Cybercriminals are always looking for vulnerabilities to exploit, so keeping your software up-to-date is one of the most effective ways to protect yourself.
McAfee Pro Tip: Always update both your software and devices. First and foremost, software updates often include patches and fixes for vulnerabilities and weaknesses that cybercriminals can exploit. By staying up-to-date, you ensure that you have the latest defenses against evolving threats. Learn more about the importance of software updates.
Final Thoughts
Phishing attempts are a constant threat in the digital world, and their sophistication continues to evolve. Cybercriminals are relying more on tailored and targeted attacks to deceive their victims. The top five most dangerous email subject lines mentioned above are a clear indicator that criminals are becoming more nuanced in their attempts to trick victims. However, with awareness and vigilance, you can effectively avoid their traps.
Remember, your personal and financial information is valuable. Make sure to protect yourself from phishing attempts by avoiding suspicious links and attachments, thinking twice before sharing your personal information, being cautious on social media, installing comprehensive security software like McAfee+, and keeping all software up-to-date. Being prepared can make all the difference in keeping your digital life secure.