Admit it. Social media has made your world a little smaller—and it’s all in the palm of your hands. Our online personas keep us connected with friends from all corners of our lives—sometimes that list of friends and followers reaches the hundreds, even thousands. From those we knew in high school, to old colleagues and PTA parents, our social circles are exploding. Who can complain about being too popular?
Social media is all about creating your online presence. Every person you add, everything you post, and every comment you like is under your control. We may not like to admit it, but according to a recent study, the average American checks their social media sites up to 17 times per day. That’s at least once a waking hour, if not more. Much of that time is spent on your mobile device, reading articles, watching viral videos, and keeping up with friends—both old and new. However, next time you scroll through your feed on your phone, don’t let your guard down; it turns out that hackers love social media just as much as you! Darn cybercriminals, always crashing the party without an invite.
Social media has become our proverbial watercooler. It is a place where we mingle with our friends and acquaintances, eagerly flipping through their photos of latte art, considering their two cents on current events, and getting valuable TV recommendations. Just like when you’re around old friends, you feel safe and comfortable, and let your guard down. Scammers take advantage of that trust and use it to their advantage through various social media phishing scams.
Reading the Signs
Cybercriminals are crafty and have no shortage of ways to get you to click a link and provide confidential information. You’d probably never knowingly give up these details online, but that’s what makes social media phishing so tricky… the signs are easy to overlook.
There’s a reason the phrase “surfing the web” exists. What starts out as a quick glance at a brand’s post can lead to a video of a cute corgi, breaking news, and oh, have you heard what that actress eats in a day? Stop what you’re doing, this is urgent! We simply follow the links and see where we end up. Often these URLs lead to credit card scams, infected sites, or malicious downloads. Thanks to link shorteners (tools that shorten a URL, often disguising the source), it’s hard to sniff out a shady link. Should you land on an infected site on your mobile phone, malware could install swiftly, putting your device, and data, at risk.
Criminals can hide their malicious links in fake giveaway posts (you know, those posts that say ten users who share will be given a grand prize!); links to “research surveys”—which again, end in a “prize;” and fake streaming videos. Criminals know their audience, so a link to the hot new George Clooney flick that just released yesterday is probably not a safe click. Just like the age old adage, if it sounds too good to be true, it probably is.
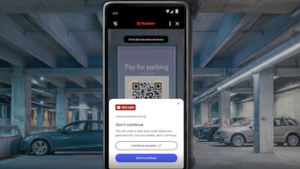
Keeping your device safe while on social media is all about using not only your heart (to like a post), but using your head. Only follow those you know and brands you trust. Be suspicious of posts that promise a free prize, and as always, think before you click. To help take some of the stress off and scroll endlessly on your mobile device in peace, download comprehensive security. McAfee® Mobile Security, free for both Android and iOS, helps to protect your device, your data, and your privacy.
Happy surfing!
Hungry for more mobile security tips? Be sure to follow @McAfee on Twitter and like us on Facebook.