Gary Davis is now a regular contributor on the Tech Nation podcast! In this episode, Gary Davis educates that phishing is more than just an innocent-looking email in your inbox and shares tips to avoid getting hooked.
The Transcript
Moira Gunn: 00:00 I’m Moira Gunn, you’re listening to Tech Nation.
Moira Gunn: 00:06 I was surprised to learn that on the internet nearly three quarters of all cyber attacks start with what’s calling a phishing email, or should we say, a fishy email. I was able to speak with regular Tech Nation contributor Gary Davis, the Chief Consumer Security Evangelist at McAfee.
Moira Gunn: 00:26 Now we always hear about phishing.
Gary Davis: 00:27 Yeah.
Moira Gunn: 00:28 It’s P-H-I-S-H-I-N-G.
Gary Davis: 00:31 Yes.
Moira Gunn: 00:32 Phishing.
Gary Davis: 00:33 Phishing with a “p”
Moira Gunn: 00:34 Not like “gone fishing”.
Gary Davis: 00:35 It’s not like gone fishing, but it’s very similar. If you think about how we fish, we put the … The concept is, let’s put a lot of lines in the water and see if we can snag a fish, right?
Moira Gunn: 00:45 Yeah.
Gary Davis: 00:45 So, it’s conceptually fishing, but it’s a different type of fishing.
Moira Gunn: 00:49 It’s phishing for you.
Gary Davis: 00:50 Yes. It’s phishing for the bad guys.
Moira Gunn: 00:52 71% of all cyber attacks start with a phishing email?
Gary Davis: 00:56 Yeah. Yeah. You know, phishing preys on, uh, our nature to, to act on email, right? We get an email, um, and, and quite honestly for, for your listeners, the, where phishing is usually most effective, targeting organizations in particular, is sending something to HR. HR is expecting to get resumes for candidates who are applying for jobs, right? More often than not, those include some sorta malicious payload which will allow them to get behind your firewall, then do something malicious in your company.
Gary Davis: 01:32 So, that’s one of the more popular techniques for, for accessing and trying to get inside a company, but yeah it just, phishing, 71% because, they know what works. They know that, that, that if they write it well enough and it looks like it’s from somebody you know and trust, that you’re gonna do the action they’re looking for, which is gonna la- enable them to get access to the information they’re trying to get access to.
Moira Gunn: 01:56 And, the initial thing they may have asked you for may not seem all that big, like, “Give us all your money,” or-
Gary Davis: 02:03 Yeah.
Moira Gunn: 02:03 “Give us all your passwords,” or, “Give us all your account,” or, “Just click here and we can resolve a fairly benign situation.”
Gary Davis: 02:11 Yeah.
Moira Gunn: 02:11 “Like we need to update the, the month and data on your credit card,” ’cause that frequently happens.
Gary Davis: 02:17 Yeah, yeah.
Moira Gunn: 02:18 You know, that your, your, your, you get a new credit card after a few years, it’s the same everything, it’s just the month and date ab- I was like, “Oh yeah. I guess so, I guess we need to … ”
Gary Davis: 02:26 Yeah.
Moira Gunn: 02:28 And it’s accounting, it’s accounting, from this global firm.
Gary Davis: 02:29 Yeah.
Moira Gunn: 02:31 You know, emailing me and saying you need to update it.
Gary Davis: 02:32 It happened to me a couple of weeks ago. I w- I was in Greece, and I was, went to the, I was staying in the Hilton there, and, you know, the, even though I’d paid using points, they said, “Well, we need a credit card for incidentals.” And they had my credit card on file. Well, typically I’m using a different credit card for, ’cause it’s usually company related, and since I was using points, I was putting it on my personal card. And, and after a little while, they call me, “Hey, look your credit card’s not working.” What do you mean it’s not working?
Gary Davis: 02:59 And, come to find out after I called my bank, it, it’d been such a long time since I accessed the application. You’re right, I got a new credit card, new, uh, expiration date, and I hadn’t updated it. But you’re right, it would be very benign to get, “Oh yeah, I do use that service, um, I should go and change it.” But that’s where d- you, this is where we, we need to change our behaviors, because instead of clicking on that email and just blindly following wherever it leads me, if I was to think, “Well geez, I need to go change my, um, my, my expiration date for Hilton.” I went to my Hilton app, opened that up and changed it in there, instead of trying to follow a link.
Moira Gunn: 03:37 So, they come at you and it’s valid, you have, what you do is you go around the other way-
Gary Davis: 03:43 Exactly.
Moira Gunn: 03:43 Have your own access, in the old days you’d say, “I’m gonna go and see the lady at the bank.”
Gary Davis: 03:46 (laughs)
Moira Gunn: 03:48 “Or the gentleman at the bank.” And now it’s like, no no, don’t go through what informs you-
Gary Davis: 03:53 Exactly.
Moira Gunn: 03:54 Whatever you do.
Gary Davis: 03:55 You think about it, e- every month we get a statement from our bank, right? And I get one from my bank, and, and I am 99.9% sure that that’s a good email. But I have trained myself not to click on that email. Instead I’ll go to my, I’ll login into my bank account, and I’ll look at my account there, because I just, I’ve conditioned myself not to click on links and email. Even if you think it’s from a known good source, because you just never know, that the bad guys are getting so good, it’s what’s called “spoofing”, where you think it’s coming from an organization but they, they’ve changed something ever so slightly that you’re going to someplace you shouldn’t be going.
Gary Davis: 04:33 So, if, if you can just teach yourself or train yourself, when you, when you get an email and you think it’s legitimate and you’re expecting it, and it’s from somebody you’d expect to get a notification from, instead of acting on the email, go directly to the source and interact that way. It’s gonna save you potentially a lot of heartache.
Moira Gunn: 04:51 And to make matters even worse, there’s different kinds of phishing.
Gary Davis: 04:54 Yeah.
Moira Gunn: 04:55 Spear phishing, whale phishing, all have-
Gary Davis: 04:58 Smishing.
Moira Gunn: 04:58 Shmishing.
Gary Davis: 04:58 (laughs)
Moira Gunn: 05:00 Oh my goodness. Okay, let’s go down through them in any order you would like.
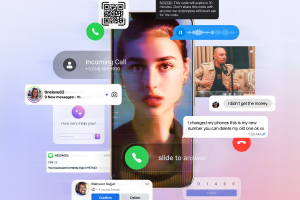
Gary Davis: 05:03 Right. Well, well smishing is probably the most, well regular phishing is, is, is simple as sending a bunch of emails out en masse, hoping that somebody’s gonna, you know, take your bait. Um, smishing is actually when they’ll send it to your phone via an SMS or text message. So, imagine getting some sort of account information to your phone, which is not that unlikely. I, almost every place I go now-
Moira Gunn: 05:25 Your, your bill is due.
Gary Davis: 05:26 Yeah, yeah. You click here to pay. “Oh okay, I’m gonna click on it ’cause I, I’m expecting it.” So, getting it on your phone, that’s called smishing. Uh, spear phishing is where you actually do what’s called social engineering, or you try to collect information about a particular group of people, and then use it to target that group.
Gary Davis: 05:44 You know, a good example is, a couple of years ago the, um, I think it was, uh, one of the NBA teams, they had gotten an email from the owner saying, “Oh, send me your user name and password because we got this special thing we wanna do for you.” Well, so they, “Of course, it’s from our owner, it’s got our logo on it.” And we go ahead and send my user name, password, which of course opened up the, the-
Moira Gunn: 06:06 (laughs)
Gary Davis: 06:06 Door, having everybody going doing whatever they want so, but they used a combination of, you know, you know, techniques that use the imagery and the tone and the social engineer- socially engineered information about the players and organization, to go do something like that.
Gary Davis: 06:24 Another, a subset of spear phishing, it’s called whale phishing, and that’s where you, you tend to focus on a high net worth individual, let’s say the CEO or some high level executive in a company using other techniques. So you, let’s say that, you know, that, that they know that the CEO is on vacation, so they, they send an email, spoof the CFO to somebody else in the organization saying, “Well the CEO told me to do this.” So all these mechanics work using high net worth individuals to go do malicious deeds.
Gary Davis: 06:57 Then there’s other types of, of phishing. There’s search engine phishing, where you would basically put up a, a, a fake search site, in order to direct people to your own search results which would in turn take you to fraudulent pages. So there, there are a variety of different techniques around phishing, all of which has the intent of trying to extract information from you, do something that you wouldn’t otherwise do, and/or in a lot of cases they’re trying to install malware on your device of, of some type.
Moira Gunn: 07:30 Now, in all those cases, I guess you could say what we might call the bleeding heart phishing, that’s out there.
Gary Davis: 07:36 It, it happens more than you might know. Whenever there is a, a major event, let’s say there’s a natural disaster, a, um, you know, we saw a lot of traffic around the Boeing Max Eight, when you had those two crashes and there was a lot of pouring out to help those in need, then they would create these fake sites and to lure people and to give them money. Um, that’s another great example.
Gary Davis: 07:59 Big sporting events, the Super Bowl, the World Cup, all these big sporting events see, um, NCAA tournament, all these events, you know, po- everybody knows, or the, the bad guys know that there’s gonna be a lot of attention given to these, so they’re gonna try to leverage those in order to try to get you to do something you wouldn’t wise- you wouldn’t otherwise do.
Gary Davis: 08:20 But that’s a great point, that you almost always try to tie it to something that’s gonna be on your mind, some sort of pop culture reference, that wouldn’t, that wouldn’t, that would motivate you to go do something. And, it’s just, it’s too bad because, you know, people typically are, are engaging with these because they feel like they genuinely wanna help. And then to know that you’re taking of that, our, our good will, I just, uh, it’s just-
Moira Gunn: 08:46 And it’s perfect because you don’t expect anything back.
Gary Davis: 08:48 Yeah. Yeah.
Moira Gunn: 08:48 It’s not like I bought something, where is it? It’s like-
Gary Davis: 08:52 Exactly. Well, in some cases for example, you may have thought, “Well I’m gonna buy tickets to the game,” or the, whatever, where, when you don’t get the tickets that would be, an, a case where that wasn’t true, but you’re right. When it comes to good will, natural disasters, you know, just relief for things that have gone on in the world, you’re right, you’re not expecting anything in return except the, the, the knowledge that you did something good, and that just, it breaks my heart when I hear about things like that.
Moira Gunn: 09:16 You know, this result pre internet, people have been doing this for a long, long, long time.
Gary Davis: 09:21 Yeah. Yeah. Although, the internet has made it very automatic now. I guess the point is the, the barrier to entry to do this has been dramatically reduced, because it’s, it’s, it doesn’t take that much effort to dupe somebody into giving you money that, that, sh- you sh- shouldn’t otherwise be getting.
Moira Gunn: 09:40 And phishing per se isn’t illegal. It’s when you take money for fraudulent ends, that’s when we get into what’s legal and illegal, right?
Gary Davis: 09:48 Well, but by nature phishing it, you’re, you’re trying to access information that you shouldn’t have access to. So I think it’s, it’s, it’s probably out, call it legally gray, but right, and it’s not until you actually give your credit card to a fraudster and something bad happens that, that you-
Moira Gunn: 10:04 When the bad happens-
Gary Davis: 10:05 Yeah.
Moira Gunn: 10:06 They’ve crossed the line.
Gary Davis: 10:07 Yeah. Then they’ll act on it. I, I remember when my identity was stolen way back in the day, um, I remember the, the, the guy who did it lived up in Pennsylvania someplace. And the way it worked back then is, they would, they got a $20,000 credit card, ringing up $18,000 over the course of two days-
Moira Gunn: 10:26 Wow.
Gary Davis: 10:26 And then the bank decided, “Well, we should go check to make sure that this guy is legit.” And, and what they’d used to do, is they would go to electronic goods stores like Best Buy, and they would buy $18,000 worth of electronic goods, then take it to a different Best Buy for cash back. So that’s how they would cash out the, the value of the credit card, knowing that it had a limited life.
Gary Davis: 10:45 And, I remember I, I got a call once, it was from the, the police department in Pennsylvania saying, “We caught the guy, you know, trying to return your goods.” Or, “The goods he bought with your credit card at a Best Buy.”
Moira Gunn: 10:58 (laughs)
Gary Davis: 10:58 And, and, they, and I said, you know, to go, go get the guy. It’s not, it’s just too much work. So, there, there, it’s really hard to motivate law enforcement, ’cause they got other things they gotta focus on. They’ve got, you know, all these other, y- you know, bad criminals doing, you know, physical harm to, to whomever. That, that they…
Moira Gunn: 11:16 And, and much higher ticket items too.
Gary Davis: 11:18 Yeah.
Moira Gunn: 11:19 You know, when they were looking at it, they might have only been looking at five or $600.
Gary Davis: 11:22 Yeah.
Moira Gunn: 11:22 Because they had to go to a lot of Best Buy’s, buy a lot of stuff-
Gary Davis: 11:26 Yeah.
Moira Gunn: 11:26 Return a lot of stuff, going back and forth, it all is pretty small-
Gary Davis: 11:30 Yeah. Exactly.
Moira Gunn: 11:30 In comparison.
Gary Davis: 11:31 Yeah. It’s, ’cause it, the, the identity thief knew not to try to in- to, to return all to one Best Buy, ’cause then that would be a, even a bigger red flag. But you’re right, if I’m a, if I’m loca- local law enforcement, “Eh, it’s just a couple hundred dollars, well I got, you know, drug dealers I gotta go break up, and bad, other bad things. So I’m gonna go focus on that, and really not focus,” so it’s just, it but, you, that doesn’t make you feel like you’re less of a victim.
Gary Davis: 11:55 Nobody wants to be a victim of scam or identity theft. Nobody ever wants to be a victim. We, we, we empathize with victims, ’cause we can put ourselves in their shoes, and it, and that’s unfortunately one of the challenges in our space is, I think a lot of the reasons why people aren’t better about things like password hygiene and, you know, checking their credit history and stuff like that, is because, well they don’t think it’s gonna happen to them, they think it’s gonna happen to somebody else. And because of that, that can be a little bit more relaxing in what I do.
Moira Gunn: 12:24 And it’s not just, uh, your hygiene, you may not be able to prevent it. I was, I stopped off an interstate and bought a couple of things, uh, ah, and gassed up at a little place, but it wasn’t the, one of the really big ones. Just happened to go in there, it was convenient there.
Gary Davis: 12:41 Yeah.
Moira Gunn: 12:41 And we were kind of in the middle of nowhere. And, for some reason, it didn’t take, put this, put this in again. So I put it in again. So, I thought, “Oh they’re probably gonna double charge me.”
Gary Davis: 12:51 Yeah.
Moira Gunn: 12:52 They didn’t double charge me, they took the card and then here I was in Northern California, and within just a few hours, someone in a, in another gas station in San Antonio, Texas, bought $115 worth of towels, shop towels, (laughs) just-
Gary Davis: 13:13 (laughs)
Moira Gunn: 13:13 Windshield wiper stuff, I mean there was just like, “doo doo doo doo doo… [counting up]
Gary Davis: 13:15 Yeah.
Moira Gunn: 13:16 So, $115 worth of that. I don’t know how I could have stopped that.
Gary Davis: 13:21 Uh, you, you can’t. That’s just it. That they’re, part of this is, y- y- we, we can do all we can do to not be a victim online, but I think a big part of the, the educational process is knowing what to do. You know, in that case, knowing to reach out to our credit card immediately and, and stopping any other transactions and, and going through the process. You’re right. There are things like that, that was probably a skimmer, that probably when they scanned it twice, they probably scanned it once for the gas that you actually bought, and there where, you know, you didn’t see it probably going through a different, um, reader.
Moira Gunn: 13:49 And I actually put it in myself.
Gary Davis: 13:50 Oh really? Okay.
Moira Gunn: 13:52 Put it in, take it out, put it in, take it out.
Gary Davis: 13:53 Hmm.
Moira Gunn: 13:53 Yeah.
Gary Davis: 13:56 You’re right.
Moira Gunn: 13:58 They’re always one step ahead.
Gary Davis: 13:59 Well, the, you know, it, it’s, they’re in it to make money, right? It’s a for profit business for lack of a better word. So, they’re always gonna be trying to figure out more effective ways to dupe people into, to, either dupe people or just take advantage of people without their knowledge, and, and do it for as long as they can.
Gary Davis: 14:15 Imagine if you didn’t quickly catch the fact that you were getting charged for stuff in San Antonio, and it went on for a week or so.
Moira Gunn: 14:21 Yeah.
Gary Davis: 14:21 They would just keep on charging, charging, charging, until, you know, either-
Moira Gunn: 14:25 It said no. (laughs)
Gary Davis: 14:26 Yeah. Well, or, or hopefully your bank would it, would realize, “Well hold on, you just used your card in Northern California,” which you would expect, and now that same card is being used to buy something in San Antonio, that, that would, you would think that your, your bank will-
Moira Gunn: 14:39 She travels fast.
Gary Davis: 14:42 (laughs)
Gary Davis: 14:42 Oh yeah.
Moira Gunn: 14:43 But not that fast.
Gary Davis: 14:43 That’s, that’s-
Moira Gunn: 14:43 There you go.
Gary Davis: 14:43 The hypersonic speed for sure.
Moira Gunn: 14:45 Hypersonic. Gary, always a pleasure. Please come back. See you soon.
Gary Davis: 14:49 I’ll do that. Thanks for having me.
Moira Gunn: 14:50 Tech Nation regular contributor Gary Davis is the Chief Consumer Security Evangelist at McAfee, the website where you can check if your email plus password has been compromised is, have I, that’s the letter I, beenpwned.com. With pawned spelled without an A. That’s P-W-N-E-D. So, it’s haveibeenpwned.com, with pawned spelled P-W-N-E-D. And that link will be on the Tech Nation website also.
Moira Gunn: 15:26 Of course when Gary said it during our conversation, he said, “haveibeenpwned.com.” And yes that’s true. Gary is from Texas, and that’s part of his charm.
Moira Gunn: 15:39 For Tech Nation, I’m Moira Gunn.