New Research: Rising Costs Are Driving Consumers to Ignore Scam Instincts for Better Deals
New McAfee research finds rising costs are driving riskier online shopping behavior, and scammers are taking advantage. Here's what consumers are encountering during major summer sales events...
Jun 09, 2026 | 6 MIN READ
- Trending Articles
-
GTA Cheat Users Exposed in Breach as Minecraft Malware Hits 116,000 Players
Jun 05, 2026 | 5 MIN READ
-
Think That Party Invite Is Real? Fake E-Vite Scams Are the New Phishing Trap
Jun 03, 2026 | 5 MIN READ
-
Are Your World Cup Tickets Legit? 40% of Fans May Risk Unofficial Sellers
Jun 01, 2026 | 10 MIN READ
How to Shop Safely During Amazon Prime Day
Amazon Prime Day scams are on the rise. Learn how to spot fake Amazon calls, delivery scams, phishing texts, and...Jun 10, 2026 | 5 MIN READ
GTA Cheat Users Exposed in Breach as Minecraft Malware Hits 116,000 Players
A GTA cheat service exposed 64,000 users while a Minecraft malware campaign infected more than 116,000 players. Here's what gamers...Jun 05, 2026 | 5 MIN READ
Think That Party Invite Is Real? Fake E-Vite Scams Are the New Phishing Trap
Fake party invitation phishing scams are on the rise. Here's how to spot them and what to do if you...Jun 03, 2026 | 5 MIN READ
Think That Party Invite Is Real? Fake E-Vite Scams Are the New Phishing Trap
Fake party invitation phishing scams are on the rise. Here's how to spot them and what to do if you...Jun 03, 2026 | 5 MIN READ
New Malware Targeting Minecraft Infects 2K Daily, and Teens are Becoming Attackers
If you or your child plays Minecraft, here's what you need to know about a large-scale malware campaign McAfee Labs...Jun 02, 2026 | 9 MIN READ
Do Windows PCs and Macs Need Antivirus Software? How McAfee Goes Beyond Built-In Security
Windows PCs and Macs include built-in security features. Learn how McAfee+ Advanced adds scam protection, identity monitoring, privacy tools, and...May 28, 2026 | 5 MIN READ
Think That Party Invite Is Real? Fake E-Vite Scams Are the New Phishing Trap
Fake party invitation phishing scams are on the rise. Here's how to spot them and what to do if you...Jun 03, 2026 | 5 MIN READ
New Malware Targeting Minecraft Infects 2K Daily, and Teens are Becoming Attackers
If you or your child plays Minecraft, here's what you need to know about a large-scale malware campaign McAfee Labs...Jun 02, 2026 | 9 MIN READ
Game Over: WeedHack – The Rise of Minecraft Malware-as-a-Service Campaigns
If you or your child plays Minecraft, here's what you need to know about a large-scale malware campaign McAfee Labs...Jun 02, 2026 | 3 MIN READ
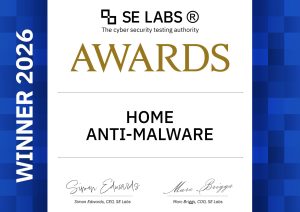
McAfee Wins SE Labs’ Highest Honor for Home Anti-Malware Protection
McAfee is proud to be recognized with the SE Labs Home Anti-Malware Award 2026, one of the most respected independent...Jun 11, 2026 | 4 MIN READ
New Research: Rising Costs Are Driving Consumers to Ignore Scam Instincts for Better Deals
New McAfee research finds rising costs are driving riskier online shopping behavior, and scammers are taking advantage. Here's what consumers...Jun 09, 2026 | 6 MIN READ
GTA Cheat Users Exposed in Breach as Minecraft Malware Hits 116,000 Players
A GTA cheat service exposed 64,000 users while a Minecraft malware campaign infected more than 116,000 players. Here's what gamers...Jun 05, 2026 | 5 MIN READ
GTA Cheat Users Exposed in Breach as Minecraft Malware Hits 116,000 Players
A GTA cheat service exposed 64,000 users while a Minecraft malware campaign infected more than 116,000 players. Here's what gamers...Jun 05, 2026 | 5 MIN READ
Think That Party Invite Is Real? Fake E-Vite Scams Are the New Phishing Trap
Fake party invitation phishing scams are on the rise. Here's how to spot them and what to do if you...Jun 03, 2026 | 5 MIN READ
New Malware Targeting Minecraft Infects 2K Daily, and Teens are Becoming Attackers
If you or your child plays Minecraft, here's what you need to know about a large-scale malware campaign McAfee Labs...Jun 02, 2026 | 9 MIN READ
McAfee Wins SE Labs’ Highest Honor for Home Anti-Malware Protection
McAfee is proud to be recognized with the SE Labs Home Anti-Malware Award 2026, one of the most respected independent...Jun 11, 2026 | 4 MIN READ
How to Shop Safely During Amazon Prime Day
Amazon Prime Day scams are on the rise. Learn how to spot fake Amazon calls, delivery scams, phishing texts, and...Jun 10, 2026 | 5 MIN READ
New Research: Rising Costs Are Driving Consumers to Ignore Scam Instincts for Better Deals
New McAfee research finds rising costs are driving riskier online shopping behavior, and scammers are taking advantage. Here's what consumers...Jun 09, 2026 | 6 MIN READ
- Trending Articles
-
GTA Cheat Users Exposed in Breach as Minecraft Malware Hits 116,000 Players
Jun 05, 2026 | 5 MIN READ
-
Think That Party Invite Is Real? Fake E-Vite Scams Are the New Phishing Trap
Jun 03, 2026 | 5 MIN READ
-
Are Your World Cup Tickets Legit? 40% of Fans May Risk Unofficial Sellers
Jun 01, 2026 | 10 MIN READ

Take control with McAfee+ Advanced
Full-service identity and credit protection now in one plan
Get McAfee+ Advanced