WannaCry, Petya, the Dyn distributed denial-of-service (DDoS) attack – all now infamous cyberattacks that have defined the modern threat landscape. The latter, which was orchestrated by Mirai malware and took the entire East Coast offline, occurred exactly a year ago, so naturally a successor has emerged. Named IoT_reaper, the new malware doesn’t necessarily depend on cracking weak passwords like Mirai did, but rather exploits vulnerabilities in various Internet of Things (IoT) devices and enslaves them into a botnet army.
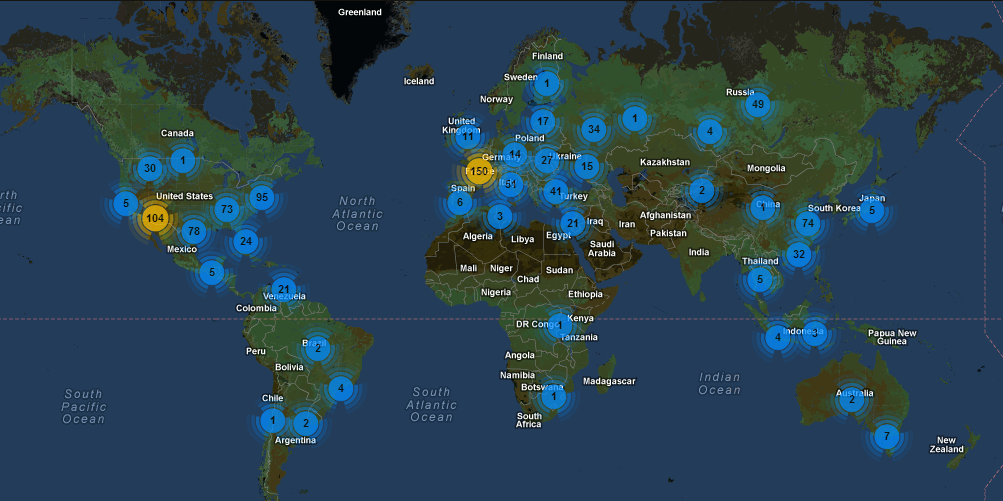
IoT_reaper leverages a total of nine vulnerabilities, to be exact. These vulnerabilities were previously disclosed in a plethora of routers and cameras that come from popular manufacturers that produce millions of devices each year. Which means there’s potential for a DDoS attack of massive proportions. In fact, researchers believe IoT_reaper is already halfway there, and has infected nearly two million devices so far. Plus, the army is growing at a mind-boggling rate of 10,000 new devices per day. For reference, it took only 100,000 infected devices for Mirai to flood the internet with traffic and take down DNS provider Dyn last year.
Tips to Improve Your Security
Clearly, it’s crucial users start thinking now about how they can prevent their IoT devices from becoming enslaved into IoT_reaper’s botnet army. To do just that, follow these tips:
- Keep security top of mind when buying an IoT device. When you’re thinking of making your next IoT purchase, make sure to do your research first. Start by looking up the device in question’s security standards. A simple Google search on the product, as well as the manufacturer, will often do the trick.
- Update your router’s firmware. Fortunately, many of the devices listed have patches available, so it’s important to immediately update your firmware if you haven’t already, as fixes are typically included within each update.
And, of course, stay on top of the latest consumer and mobile security threats by following me and @McAfee_Home on Twitter, and ‘Like’ us on Facebook.