It has been two weeks since the announcement by multiple global law enforcement agencies regarding the takedown of the communications infrastructure for the Trojans GameOver Zeus and Cryptolocker. Judging by the number of downloads for the McAfee Stinger utility, thousands of systems worldwide no longer provide money to Evgeniy Mikhailovich Bogachev and his associates.
However, managing the cleanup across multiple systems can be an onerous task. For those responsible for managing many systems, running the McAfee Stinger in a systematic fashion across all devices is simply not an option. Infected systems that connect to one of the sinkholes will also make a connection to the following IP address: 72.52.116.52:4643.
What to Do
McAfee recommends that system managers not block or filter this address because it acts as a useful indicator for infected devices, and connecting to this address does not introduce any risk.
With this information, it is possible to configure your security products to alert you should any of your systems attempt to connect to this IP address and port number. McAfee Enterprise Security Manager (see Figure 1) provides real-time visibility into all activity across systems, networks, databases, and applications. McAfee Enterprise Security Manager provides real-time situational awareness, and this rule allows organizations to respond intelligently and efficiently in mitigating GameOver Zeus and Cryptolocker infections.
 Figure 1: McAfee Enterprise Security Manager.
Figure 1: McAfee Enterprise Security Manager.
In order to detect whether any systems are attempting to connect to this lighthouse IP address, an alert can be created that will generate an alarm when the rule is activated (see Figure 2):
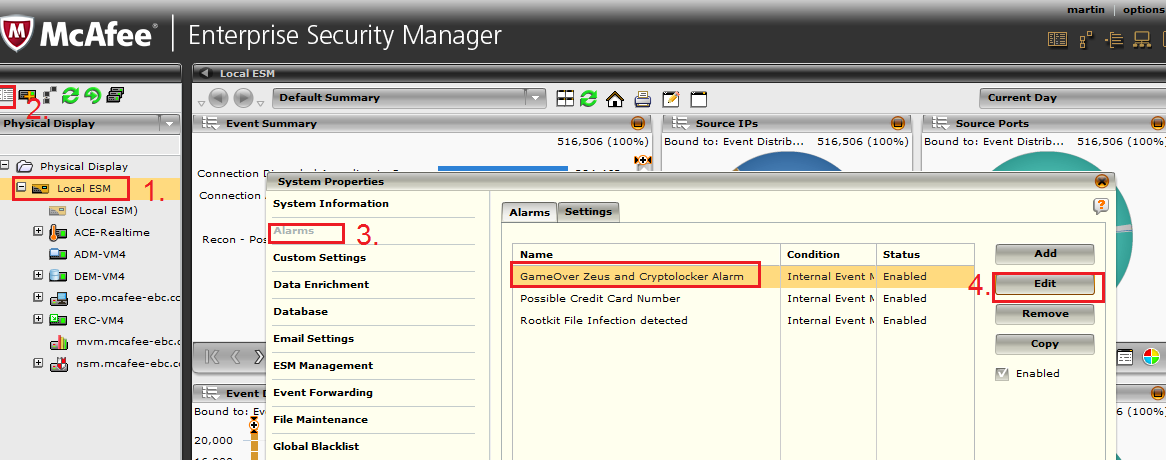 Figure 2: A McAfee Enterprise Security Manager alarm.
Figure 2: A McAfee Enterprise Security Manager alarm.
When activated, the alarm will inform the system administrator which system is likely infected. This provides an opportunity to focus your removal efforts using an efficient means to address GameOver Zeus and Cryptolocker infections.
Thanks to Martin DeJongh, Enterprise Technology Architect, for his assistance with this post and guidance.











