Mobile banking Trojans have usually pretended to be security applications (for example, Zitmo) or legitimate banking apps (FakeToken or FkSite a.k.a. Perkele) to trick users into installing the malware. These apps steal incoming SMS messages that could contain mTANs (Mobile Transaction Authentication Numbers) used as two-factor authentication to allow Internet transactions. Now, however, it seems that malware authors are adding a new social-engineering trick to improve the rate of malware installations–by taking advantage of one of the biggest and most popular social networks.
Despite the fact that Facebook two-factor authentication has been available since May 2011, currently there is no official stand-alone application to generate one-time passwords similar to the mobile app Google Authenticator. Instead, Facebook delivers the second factor of authentication via two functions:
- Login approvals: If it is enabled, Facebook will send a text message with the security code to the mobile phone number configured in your profile (contact information) every time you try to log in from an unknown device.
- Code generator: For when you are traveling and can’t receive text messages. If this function is activated, you can get a security code by going to the option “Code Generator” in the Facebook mobile app.
Recently McAfee Labs received a mobile malware sample that, at first sight, seems to be just another variant of the Android Trojan iBanking, but in fact is an improved version of the malware. Instead of pretending to be a legitimate banking or security app, this version poses as an official Facebook app that provides a “password token” to protect the account from hijacking by adding another authentication factor. Once the malware is installed, the following icon appears in the home launcher of the device:
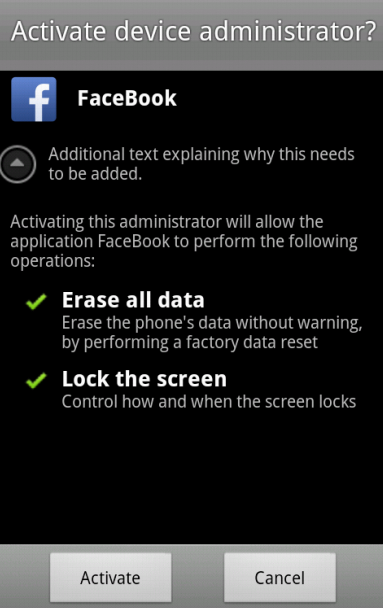
Unlike the official Facebook app, the malware uses the word FaceBook with a capital B. If you notice the change in style, that should trigger an alarm. In order to make dynamic analysis difficult, the app will not work if the IMEI, phone number, network operator and SIM serial number values are the same as those configured by default in an Android emulator. On the other hand, if the app is executed in a real device, it will ask for device administrator privileges to make the removal of the app more difficult:
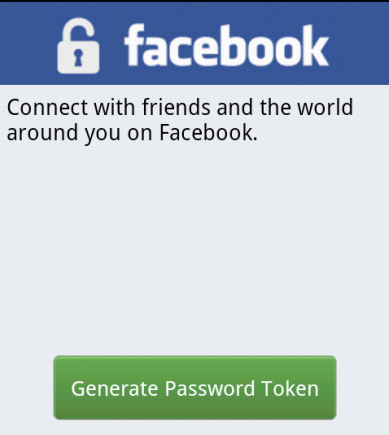
Another suspicious characteristic is the text “Additional text explaining why this needs to be added,” which shows that this version of the malware is currently under development. After the app is activated by the device administrator, the malware shows the following user interface–pretending to be a Facebook password-token generator:
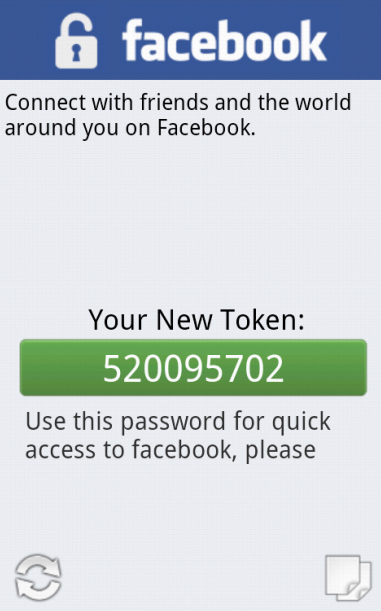
When the user clicks on the button Generate Password Token, the app simulates the generation of the security code to finally provide the “New Token” that should be used to access your Facebook account:
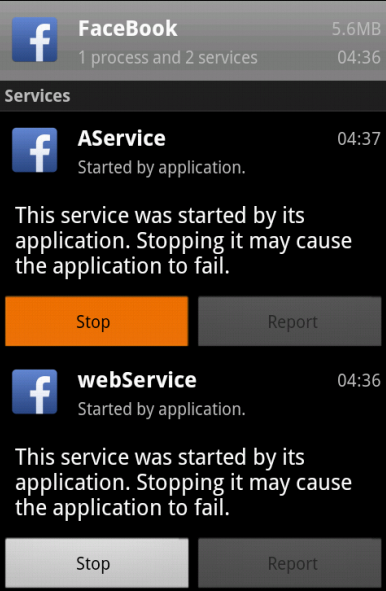
The provided security code will not work in Facebook because it is a fake number generated by a custom algorithm based on the device identifier (IMEI) or random numbers. At the same time, the malware will start two services that will run in the background without the user’s consent:
iBanking Variant’s Malicious Actions
Just like older variants of iBanking, this variant can also execute commands sent by the attacker via SMS or HTTP to perform any of the following actions:
- Intercept incoming SMS messages (that could include mTAns) and forward them to the attacker
- Forward all incoming calls to a phone number specified in the malware
- Steal all the SMS messages in the inbox and sent folders
- Steal all the call logs (incoming/Outgoing/missed calls)
- If the app was added as a Device Administrator, the malware will attempt to erase all user data by asking the user to do so. External storage such as SD cards will not be affected.
- Record the surrounding audio captured by the microphone to store it in the SD card and later send it to a remote server
- Send a text message, with the body provided by the attacker, to the number
- Steal the contact list
- Steal all the images (jpg, jpeg, gif and png) stored in the SD card
- Leak the GPS location of the infected device
- Report all installed applications in the device
- Start the malicious services and send a text message to the attacker with the SIM serial number, manufacturer, and model of the infected device
Taking into account the existence of security vulnerabilities such as Heartbleed, which allows the remote extraction of sensitive data such as user names and passwords, it is clear that only one password is not enough to protect access to online services. For that reason multifactor authentication systems are becoming more popular every day as an additional security measure to prevent the hijacking of online accounts. This variant of iBanking shows that malware authors are aware of this step and have started to associate with social networks to trick users into installing their malware.
McAfee Mobile Security detects this Android threat as Android/iBanking.B and alerts mobile users if it is present, while protecting them from any data loss. For more information about McAfee Mobile Security, visit https://www.mcafeemobilesecurity.com.