Authored by Oliver Devane, Vallabh Chole, and Aayush Tyagi
McAfee has recently observed several malicious Chrome Extensions which, once installed, will redirect users to phishing sites, insert Affiliate IDs and modify legitimate websites to exfiltrate personally identifiable information (PII) data. According to the Google Extension Chrome Store, the combined install base is 100,000
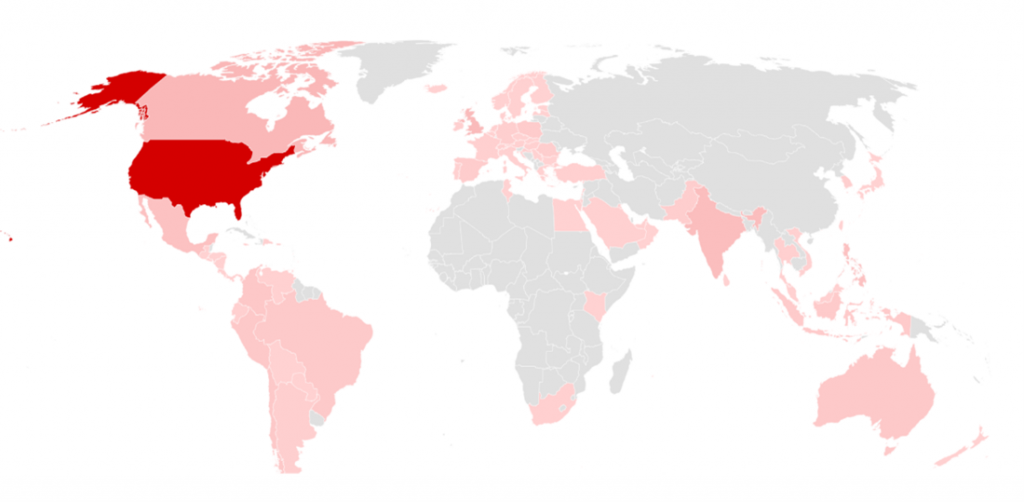
McAfee Labs has observed these extensions are prevalent in USA, Europe and India as we can observe in the heatmap below.
The perpetrator targets over 1,400 domains, where 100 of them belong to the top 10,000 Alexa ranking including hbomax.com, hotels.com and expedia.com.
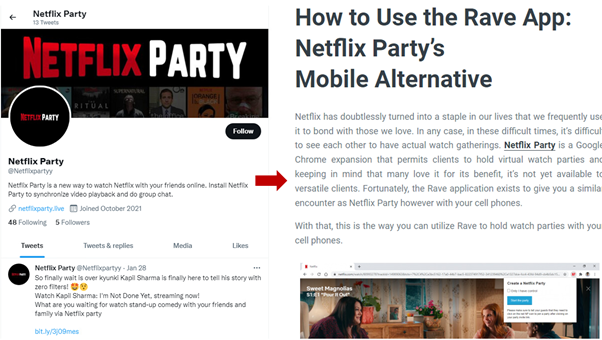
One extension, ‘Netflix Party’, mimics the original Netflix Party extension, which allows groups of people to watch Netflix shows at the same time. However, this version monitors all the websites you visit and performs several malicious activities.
The malicious actor behind the extensions has created several Twitter accounts and fake review websites to deceive users into trusting and installing the extensions.
The victim will be tricked into installing the extension and their data will be stolen when browsing a gift card site.
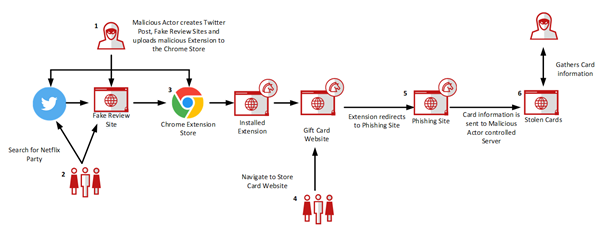
The details of each step are as follows:
- The perpetrator creates malicious extensions and adds them to the Chrome Extension Store. They create fake websites to review the extensions and fake Twitter accounts to publicize them.
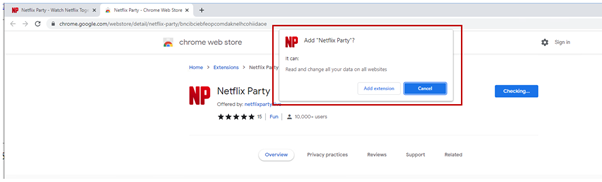
- A victim may perform a web or Twitter search for Netflix Party, read the review and click on a link that will lead them to the Google Chrome Store.
- They click to install the Extension and accept the permissions.
- The victim will either perform a web search or directly navigate to the gift card website. The Extension will identify the website and redirect them to the phishing page.
- The victim will enter their gift card information on the phishing page.
- The gift card information is posted to the server to which the malicious actor has access. They can now use or sell the stolen data and the victim will lose their funds.
Technical Analysis
This section contains the technical analysis of the malicious chrome extension “bncibciebfeopcomdaknelhcohiidaoe“.
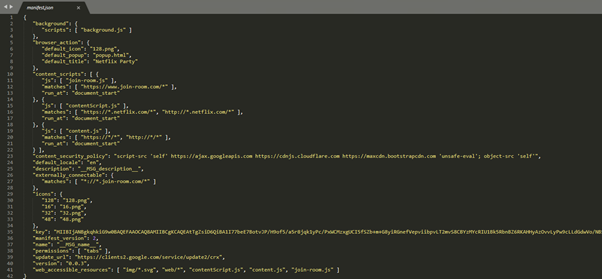
Manifest.json
The manifest.json file contains the permissions of the extension. The ‘unsafe-eval’ permission in the ‘content_security_policy’ and the allowed use of content.js on any website visited by the user is of particular concern
Background.js
When the extension is installed, the background.js script will be loaded. This file uses a simple obfuscation technique of putting all the code on one line which makes it difficult to read. This is easily cleaned up by using a code beautifier and the image below shows the obfuscated script on the first line and the cleaned-up code below the red arrow.
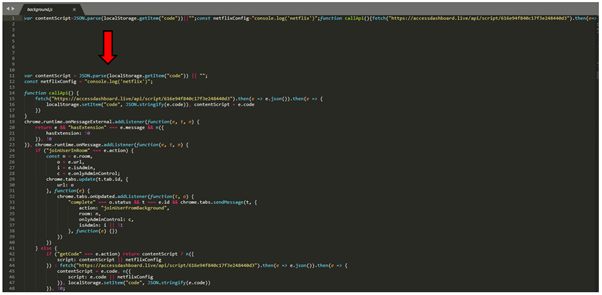
This script accesses https://accessdashboard[.]live to download a script and store it as variable ‘code’ in Chrome’s local storage. This stored variable is then referenced in the content.js script, which is executed on every visited website.
Content.js
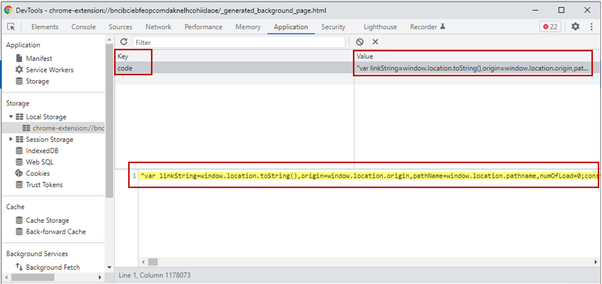
After beautification, we see the code will read the malicious script from the ‘code’ variable which was previously stored.

‘Code’
The malicious code has three main functions, redirection for phishing, modifying of cookies to add AffiliateIDs, and modifying of website code to add chat windows.
![]()
Redirection for Phishing
Redirection for phishing works by checking if the URL being accessed matches a list, and conditionally redirects to a malicious IP that hosts the phishing site.
URLs monitored are:
- https[:]//www.target.com/guest/gift-card-balance
- https[:]//www.macys.com/account/giftcardbalance
- https[:]//www.nike.com/orders/gift-card-lookup
- https[:]//www.nordstrom.com/nordstrom-gift-cards
- https[:]//www.sephora.com/beauty/giftcards
- https[:]//www.sephoragiftcardbalance.com
- https[:]//balance.amexgiftcard.com
- https[:]//prepaidbalance.americanexpress.com/GPTHBIWeb/validateIPAction.do?clientkey=retail%20sales%20channel
- https[:]//amexprepaidcard.com
- [:]//secure4.store.apple.com/shop/giftcard/balance
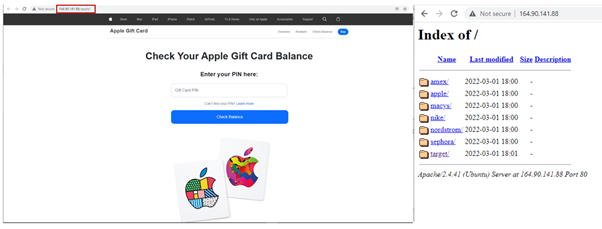
Upon navigating to one of the above sites, the user will be redirected to 164[.]90[.]144[.]88. An observant user would notice that the URL would have changed to an IP address, but some users may not.
The image below shows the Apple Phishing site and the various phishing kits being hosted on this server.
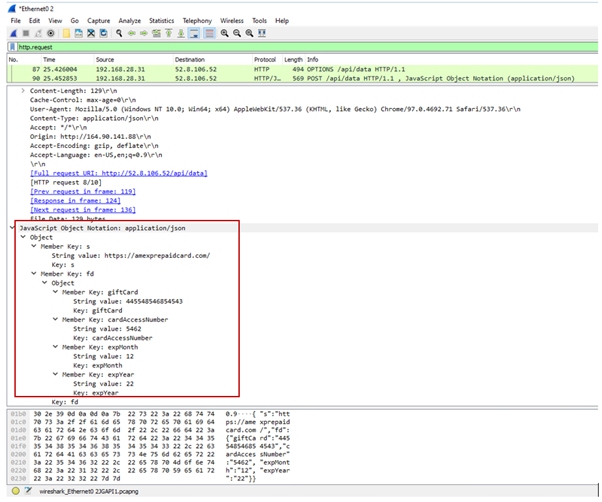
The phishing sites share similar codes. If a user enters their gift card information, the data will be posted to 52.8.106.52. A network capture of the post request is shown below:
Modifying of cookies to add AffiliateIDs
The second malicious function contains AIPStore which is a dictionary containing a list of URLs and their respective monetizing sites which provide affiliate IDs. This function works by loading new tabs which will result in cookies being set on the visited sites. The flow below describes how the extension will work.
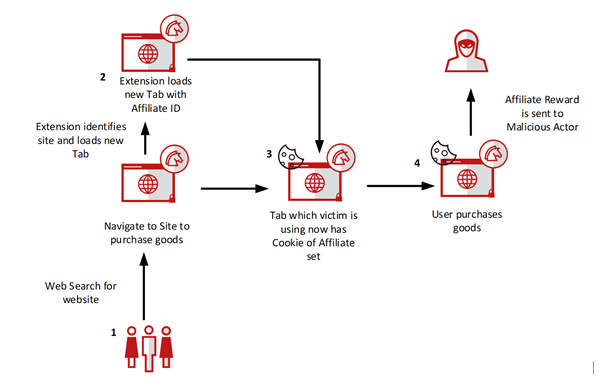
- A user navigates to a retail website
- If the retail website is contained in the AIPStore keymap, the extension will load a new tab with a link to a monetizing site which sets the cookie with the affiliate ID. The new tab is then closed, and the cookie will persist.
- The user will be unaware that a cookie would have been set and they will continue to browse the website.
- Upon purchasing any goods, the Affiliate ID will be recognized by the site vendor and commission will be sent to the Affiliate ID owner which would be the Malicious Actor
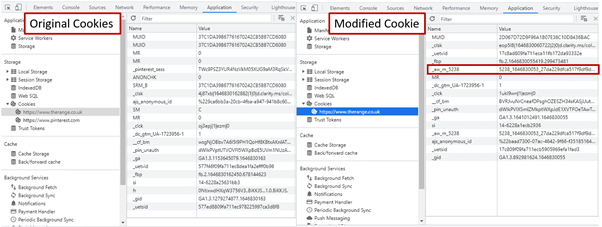
The left image below shows the original site with no affiliate cookie, the one on the right highlights the cookie that has been added by the extension.
Chat Windows
The final function checks a list of URLs being accessed and if they match, a JS script will be injected into the HTML code which will result in a chat window being displayed. The image below shows the injected script and the chat window.
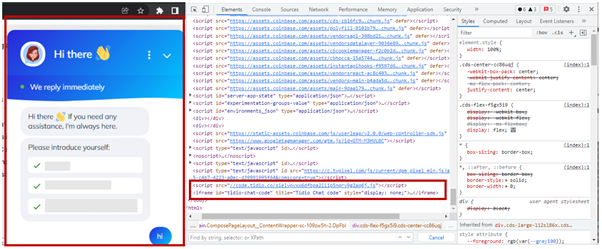
The chat window may be used by the malicious actor to request PII data, credit card, and product key information.
Conclusion
This threat is a good example of the lengths malicious actors will go to trick users into installing malware such as creating Twitter accounts and fake review websites.
McAfee advises its customers to be cautious when installing Chrome Extensions and pay attention to the permissions that they are requesting.
The permissions will be shown by Chrome before the installation of the Extension. Customers should take extra steps to verify the authenticity if the extension is requesting permissions that enable it to run on every website you visit such as the one detailed in this blog
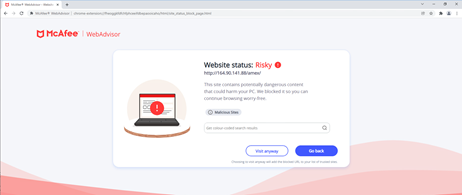
McAfee customers are protected against the malicious sites detailed in this blog as they are blocked with McAfee WebAdvisor as shown below.
The Malicious code within the extension is detected as Phish-Extension. Please perform a ‘Full’ scan via the product.
| Type | Value | Product | Detected |
| URL – Phishing Sites | 164.90.141.88/* | McAfee WebAdvisor | Blocked |
| Chrome Extension | netflix-party – bncibciebfeopcomdaknelhcohiidaoe | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | teleparty – flddpiffdlibegmclipfcnmaibecaobi | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | hbo-max-watch-party – dkdjiiihnadmgmmfobidmmegidmmjobi | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | prime-watch-party – hhllgokdpekfchhhiknedpppjhgicfgg | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | private-watch-party – maolinhbkonpckjldhnocgilkabpfodc | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | hotstar-ad-blocker – hacogolfhplehfdeknkjnlblnghglfbp | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | hbo-ad-blocker – cbchmocclikhalhkckeiofpboloaakim | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | blocksite – pfhjfcifolioiddfgicgkapbkfndaodc | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | hbo-enhanced – pkdpclgpnnfhpapcnffgjbplfbmoejbj | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | hulu-watch-party – hkanhigmilpgifamljmnfppnllckkpda | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | disney-plus-watch-party – flapondhpgmggemifmemcmicjodpmkjb | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | spotify-ad-blocker – jgofflaejgklikbnoefbfmhfohlnockd | Total Protection and LiveSafe | Phish-Extension |
| Chrome Extension | ott-party – lldibibpehfomjljogedjhaldedlmfck | Total Protection and LiveSafe | Phish-Extension |












