Authored by Dexter Shin
Instagram has become a platform with over a billion monthly active users. Many of Instagram’s users are looking to increase their follower numbers, as this has become a symbol of a person’s popularity. Instagram’s large user base has not gone unnoticed to cybercriminals. McAfee’s Mobile Research Team recently found new Android malware disguised in an app to increase Instagram followers.
How can you increase your followers or likes?
You can easily find apps on the internet that increase the number of Instagram followers. Some of these apps require both a user account and a password. Other types of apps only need the user to input their user account. But are these apps safe to use?
Many YouTubers explain how to use these apps with tutorial videos. They log into the app with their own account and show that the number of followers is increasing. Among the many videos, the domain that appears repeatedly was identified.
The way the domain introduces is very simple.
- Log in with user account and password.
- Check credentials via Instagram API.
- After logging in, the user can enjoy many features provided by the app. (free followers, free likes, unlimited comments, etc.)
- In the case of free followers, the user needs to input how many followers they want to gain.

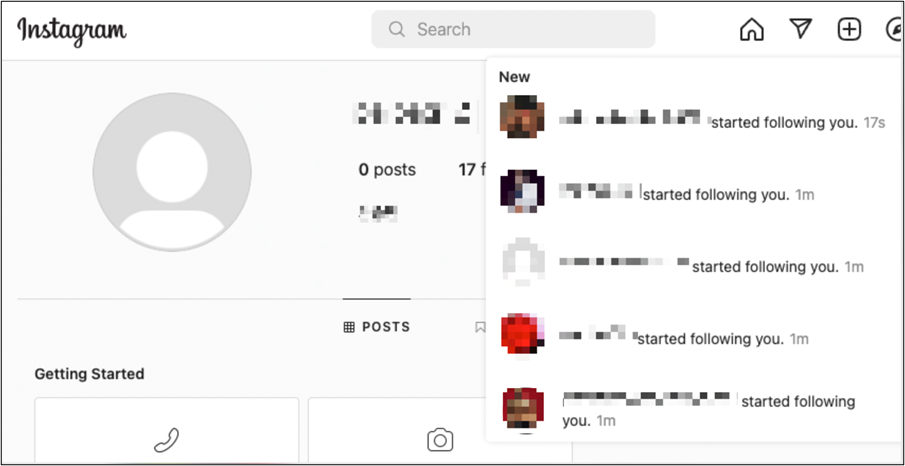
When you run the function, you can see that the number of followers increases every few seconds.
How does this malware spread?
Some Telegram channels are promoting YouTube videos with domain links to the malware.
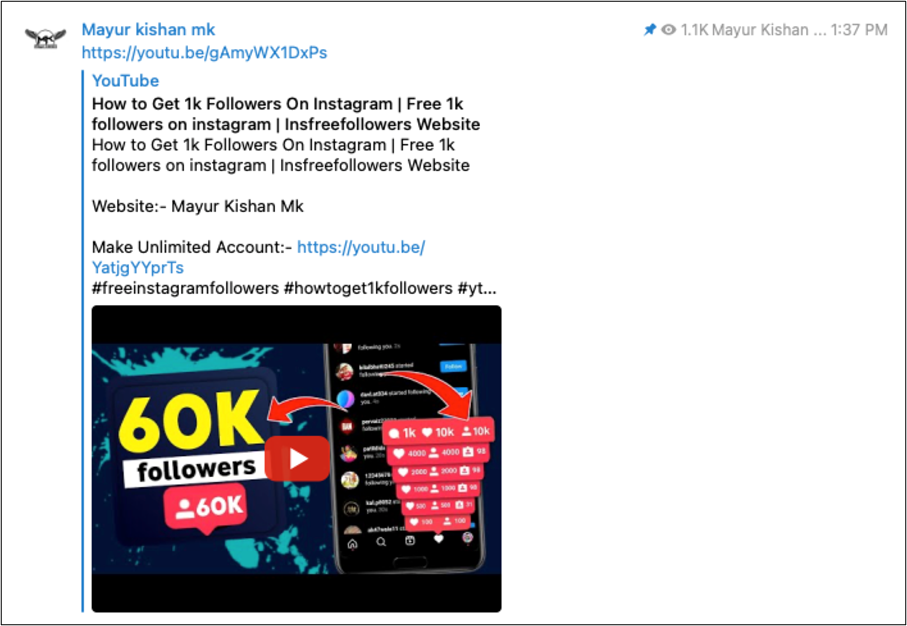
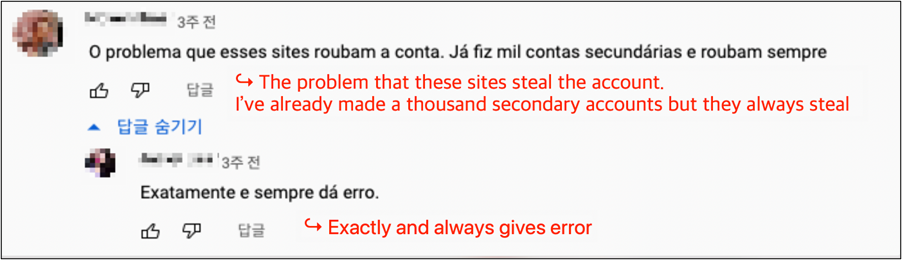
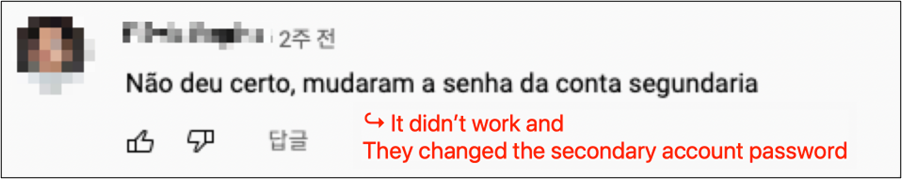
We have also observed a video from a famous YouTuber with over 190,000 subscribers promoting a malicious app. However, in the video, we found some concerning comments with people complaining that their credentials were being stolen.
Behavior Analysis in Malware
We analyzed the application that is being promoted by the domain. The hidden malware does not require many permissions and therefore does not appear to be harmful. When users launch the app, they can only see the below website via the Android Webview.
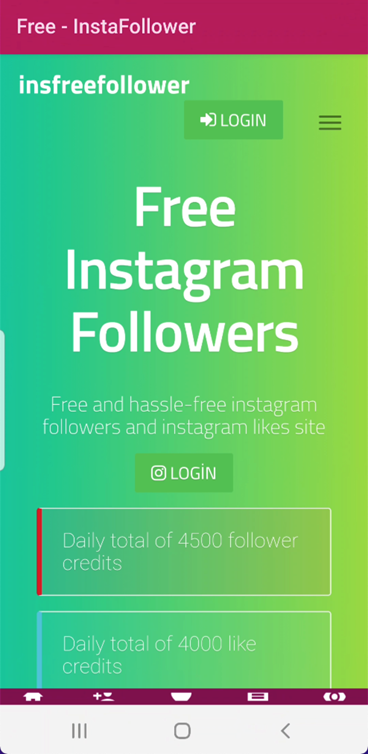
After inspecting the app, we observe the initial code does not contain many features. After showing an advertisement, it will immediately show the malicious website. Malicious activities are performed at the website’s backend rather than within the Android app.

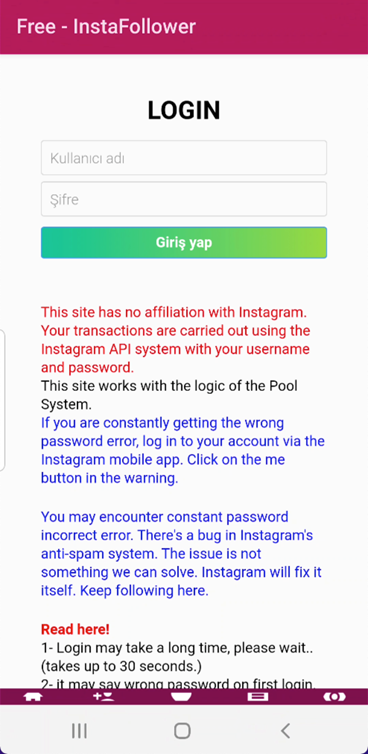
The website says that your transactions are carried out using the Instagram API system with your username and password. It is secure because they use the user’s credentials via Instagram’s official server, not their remote server.
Contrary to many people’s expectations, we received abnormal login attempts from Turkey a few minutes after using the app. The device logged into the account was not an Instagram server but a personal device model of Huawei as LON-L29.
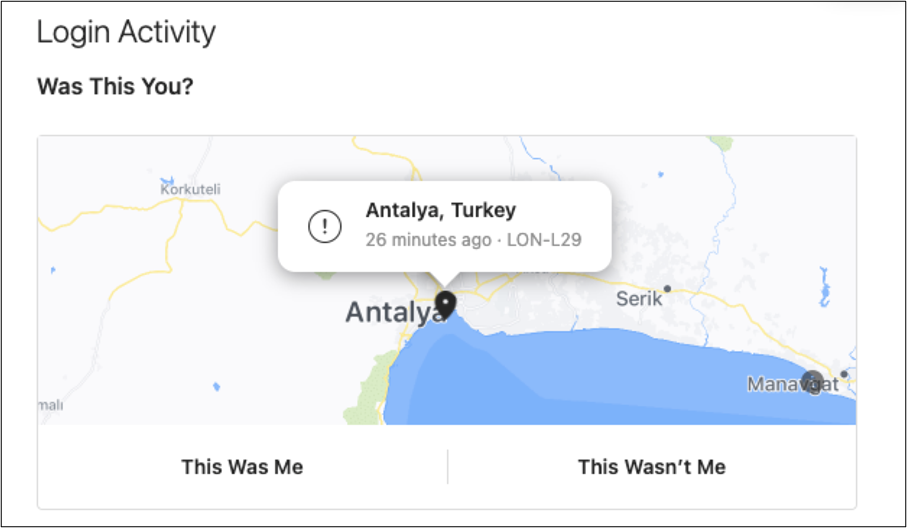
As shown above, they don’t use an Instagram API. In addition, as you request followers, the number of the following also increases. In other words, the credentials you provided are used to increase the number of followers of other requesters. Everyone who uses this app has a relationship with each other. Moreover, they will store and use your credentials in their database without your acknowledgement.
How many users are affected?
The languages of most communication channels were English, Portuguese, and Hindi. Especially, Hindi was the most common, and most videos had more than 100 views. In the case of a famous YouTuber’s video, they have recorded more than 2,400 views. In addition, our test account had 400 followers in one day. It means that at least 400 users have sent credentials to the malware author.
Conclusion
As we mentioned in the opening remarks, many Instagram users want to increase their followers and likes. Unfortunately, attackers are also aware of the desires of these users and use that to attack them.
Therefore, users who want to install these apps should consider that their credentials may be leaked. In addition, there may be secondary attacks such as credential stuffing (=use of a stolen username and password pairs on another website). Aside from the above cases, there are many unanalyzed similar apps on the Internet. You shouldn’t use suspicious apps to get followers and likes.
McAfee Mobile Security detects this threat as Android/InstaStealer and protects you from this malware. For more information, visit McAfee Mobile Security.
Indicators of Compromise
SHA256:
- e292fe54dc15091723aba17abd9b73f647c2d24bba2a671160f02bdd8698ade2
- 6f032baa1a6f002fe0d6cf9cecdf7723884c635046efe829bfdf6780472d3907
Domains:
- https[://]insfreefollower.com












